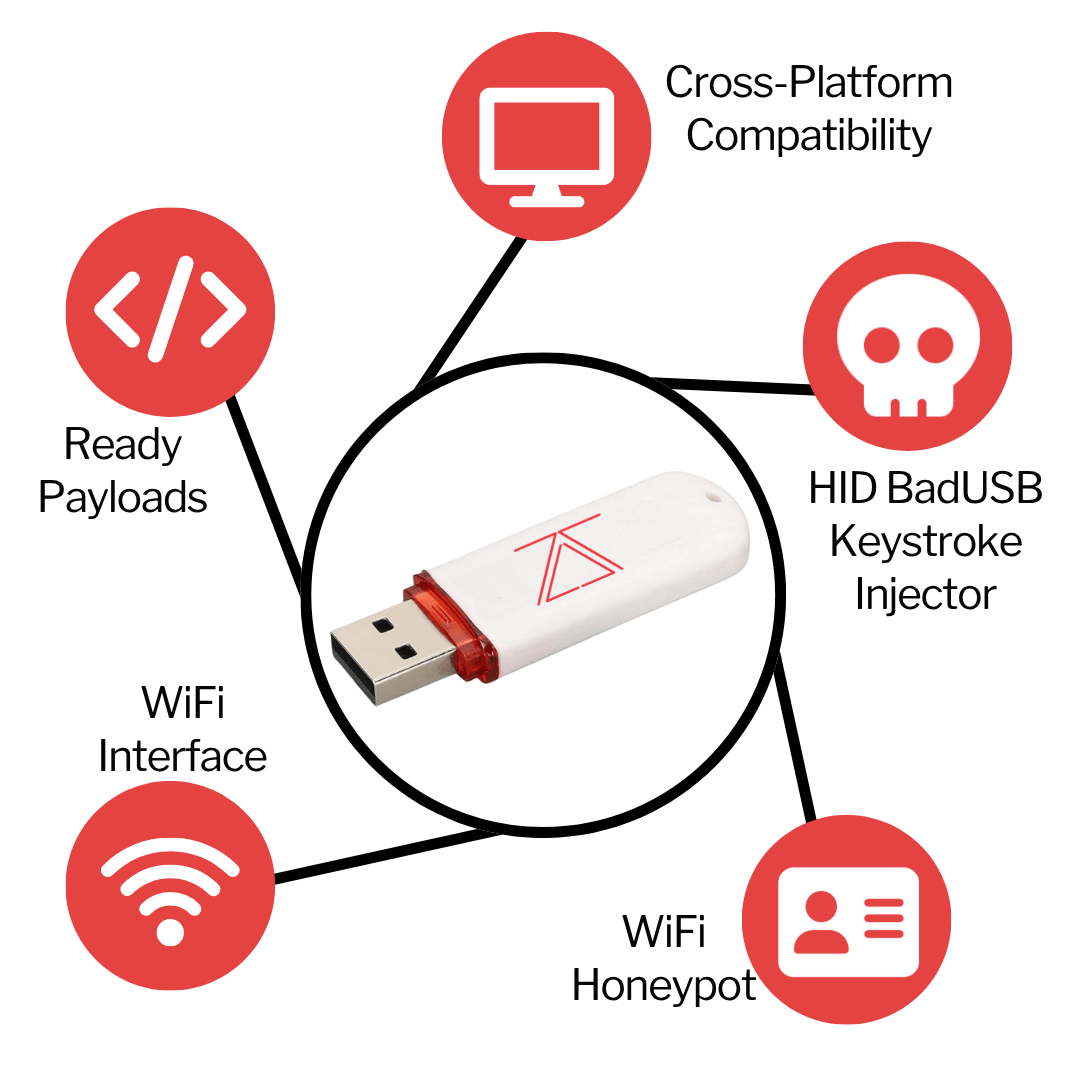
HID BadUSB Keystroke Injector
Ready Payloads
Wi-Fi Interface
Wi-Fi Honeypot
Cross-Platform Compatibility
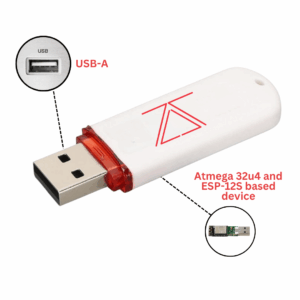
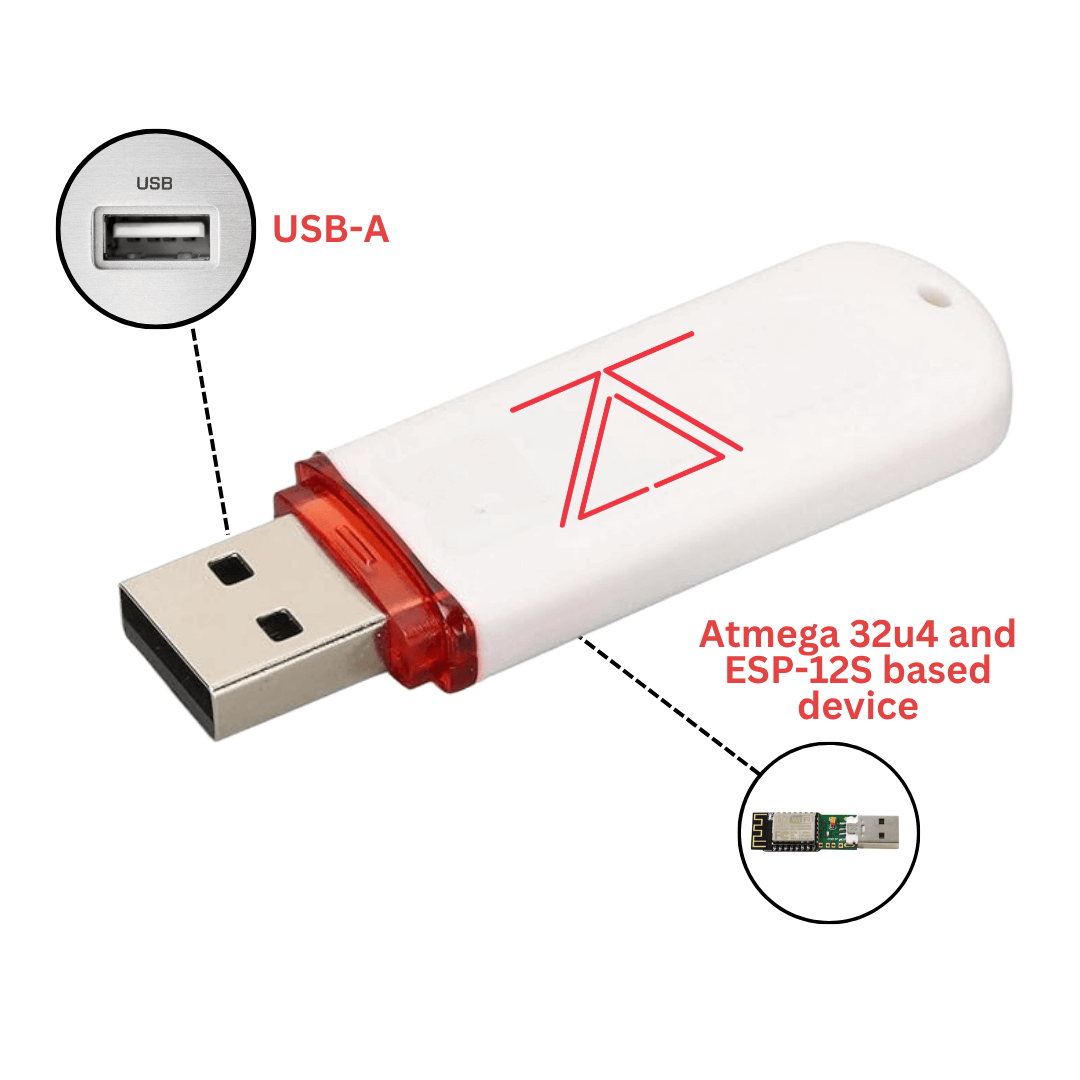
ZS Cactus WiFi Keystroke Injection BadUSB
The ZS Cactus combines keystroke injection capabilities and Wi-Fi phishing with wireless control for comprehensive security assessments.



Compare ZS CactusPRO vs ZS Cactus
ZS Cactus PRO = ZS Cactus + Hardware Keylogger
Key Features
- HID Keystroke Injection: Emulates a keyboard and inject automated keystrokes via USB or Wi-Fi to hack the target, steal data from it or remotely control it.
- Ready Payloads: Get instant access, steal credentials, browser data and even Wi-Fi passwords with a few clicks.
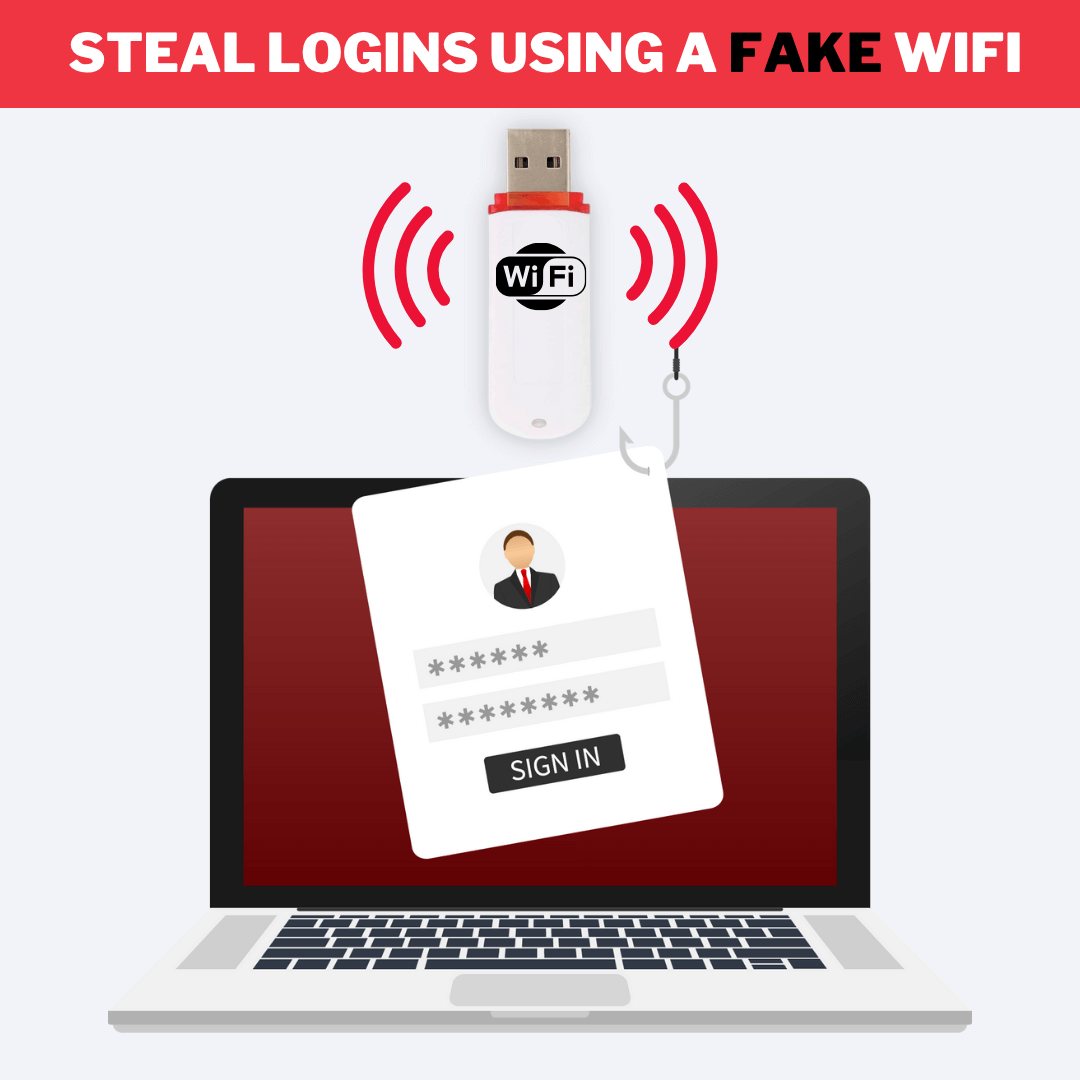
- Wi-Fi Honeypot: Create a fake/rogue wireless network to steal login information from connected devices.
- Web Interface: Launch attacks, control and manage everything through a mobile-friendly web interface..
- Remote Mouse & Keyboard Control: Remotely controls cursor movement and keystroke input.
- Wireless Payload Execution: Delivers and triggers payloads over Wi-Fi connections for remote deployment.
- Direct Data Extraction: Retrieves or exfiltrates files and data via URL, FTP, or similar transfer protocols.
- Multi-Platform Compatibility: Works with Windows, Linux, and Apple Mac OS
Applications
- Hack computers using built-in or own payloads using BadUSB attacks.
- Steal login information of Facebook, Instagram, Linkedin and more using the Fake Wi-Fi Honeypot.
- Control everything remotely using a web-interface from any device with a web browser!

Setting up your ZS Cactus
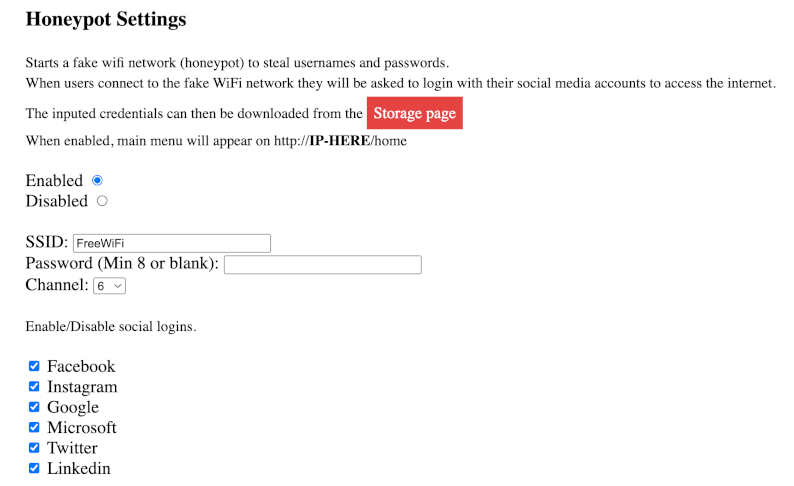
Honeypot Mode
This mode can be used to steal login credentials. It creates a fake WiFi network that asks clients to login using their social media account to access the internet. It can also be configured to serve custom HTML pages to hook the connected clients to BeEF or steal other data.
Connect to the fake access point, disregard the login prompt and navigate to http://192.168.1.1/home to access the command center. Navigate to “Storage” and you should have a file named “honeypot-log.txt”.
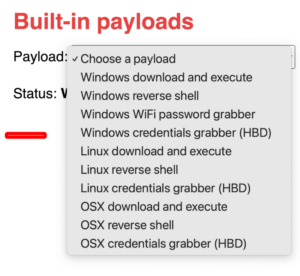
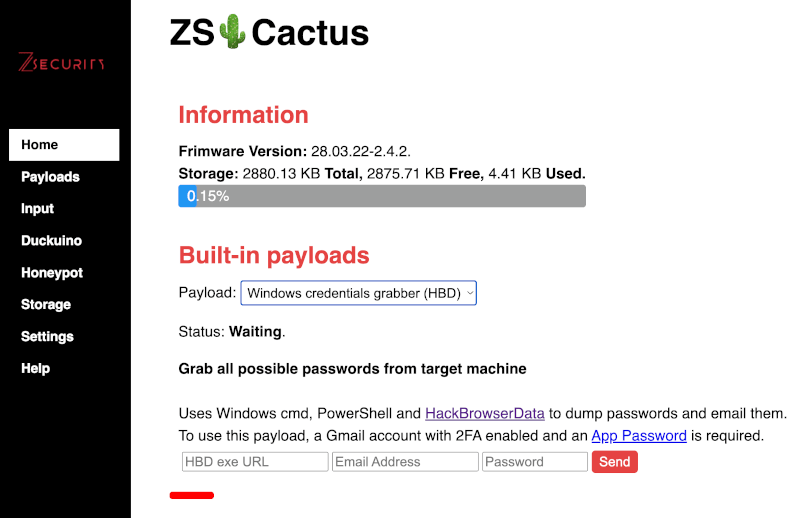
Built-in Payloads
ZS Cactus comes with 10 built-in payloads for Windows, Linux and OSX.
These payloads can be used to gain full control over the target system, steal browser data including saved passwords, steal stored Wi-Fi passwords and even download and execute any file you want!
Wi-Fi Control Center
ZS Cactus can be configured and controlled over Wi-Fi using a mobile-friendly web interface. Simply connect the device to a USB power supply and connect to it’s Wi-Fi network “ZSCactus“. The default password which can be changed from the settings is “zscactus“. Once connected open up a web browser and navigate to http://192.168.1.1/ to access the control center. The default credentials are “admin” / “zscactus”.
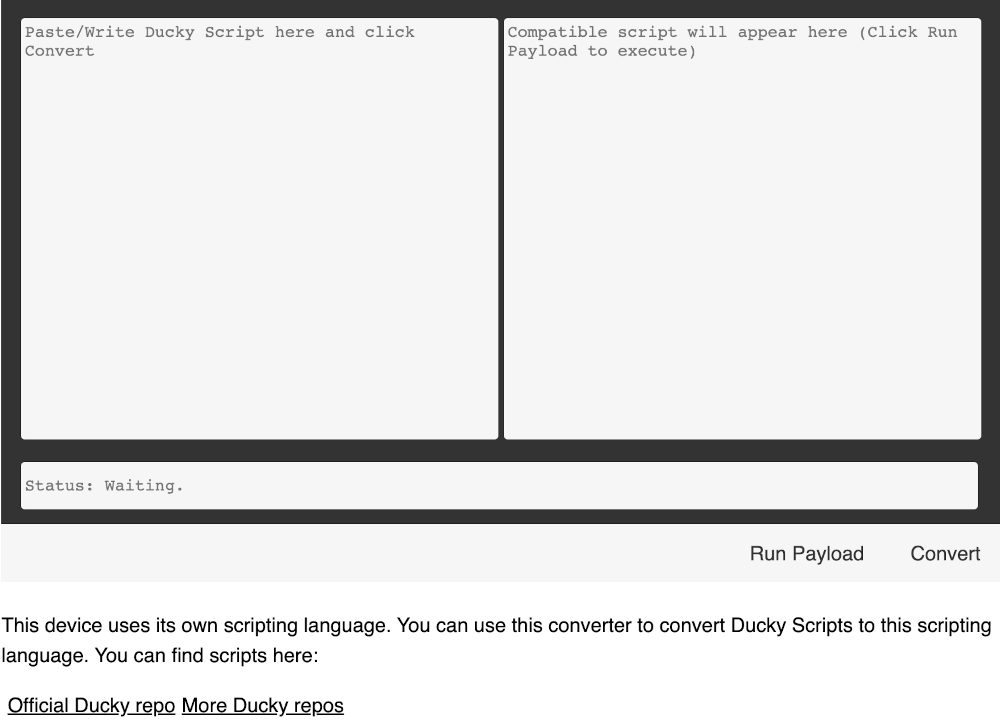
Payloads
This page allows you to manage your payloads, you can upload, run or delete custom payloads.
You can also set a payload to auto run when the device is connected to a computer.
How to use your ZS Cactus to Hack Windows
Complete your Pentesting Tool Set with our Bundle
Hacker Starter Kit
Save $15 with this bundle
► + Free 1 Month zSecurity Trial VIP membership.
$99.97
BadUSB Silent Intrusion Kit
Save $10 with this bundle
► + Free 1 Month zSecurity Trial VIP membership.
$59.97
BadUSB Silent Intrusion Kit Plus
Save $10 with this bundle
► USB Data Blocker
► + Free 1 Month zSecurity Trial VIP membership.
$69.97
FAQ
What's the difference between the ZS Cactus and other WiFi BadUSB devices outhere?
What do you use the ZS Cactus WiFi Keystroke Injection BadUSB for?
Ethical Hackers and Cybersecurity Experts use the ZS Cactus WiFi Keystroke Injection BadUSB for various purposes, including simulating USB-based attacks, testing endpoint and physical security, conducting social engineering exercises, raising user awareness, and assessing incident response capabilities, among other critical security functions!
Can antivirus software detect and block ZS Cactus WiFi Keystroke Injection BadUSB attacks?
BadUSB attacks operate at the firmware level, which is much harder for standard antivirus software to detect, as the device appears to the operating system as a legitimate keyboard.



























Reviews
There are no reviews yet.