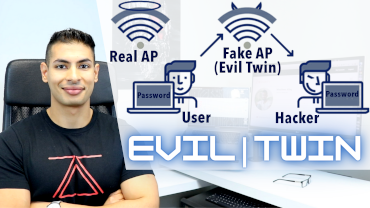
Hack WPA / WPA2 WiFi Without Wordlist Using Evil Twin Attack
This video shows how to manually create an evil twin network to steal WiFi password / key of a target network. The same method can be used to start a normal fake AP / honeypot for other uses.
Resources:
PS: This video is made for educational purposes only, all the devices / machines / networks used in it are owned by the author, therefore the author has full permissions test what’s demonstrated, please do not do this on systems that you do not own or have permission to test.
Leave A Reply
You must be logged in to post a comment.




15 Comments
root@kali:~/fap# hostapd hostapd.conf
Configuration file: hostapd.conf
nl80211: Could not configure driver mode
nl80211: deinit ifname=wlan0mon disabled_11b_rates=0
nl80211 driver initialization failed.
wlan0mon: interface state UNINITIALIZED->DISABLED
wlan0mon: AP-DISABLED
wlan0mon: CTRL-EVENT-TERMINATING
hostapd_free_hapd_data: Interface wlan0mon wasn’t started
it shows this, please tell me sir what will i do ?
Can some somebody send me the web template that was used in that vedio for evil twin attack I am struggling for that template please there is no link in the description for downloading that template
Please 🙏 some one send
i m also getting above issue
root@kali:~/fap# hostapd hostapd.conf
Configuration file: hostapd.conf
nl80211: Could not configure driver mode
nl80211: deinit ifname=wlan0mon disabled_11b_rates=0
nl80211 driver initialization failed.
wlan0mon: interface state UNINITIALIZED->DISABLED
wlan0mon: AP-DISABLED
wlan0mon: CTRL-EVENT-TERMINATING
hostapd_free_hapd_data: Interface wlan0mon wasn’t started
Even I am getting the same error
configuration file: hostapd.conf
nl80211: Could not configure driver mode
nl80211: deinit ifname=wlan0mon disabled_11b_rates=0
nl80211 driver initialization failed.
wlan0: interface state UNINITIALIZED->DISABLED
wlan0: AP-DISABLED
wlan0: CTRL-EVENT-TERMINATING
hostapd_free_hapd_data: Interface wlan0 wasn’t started
did u figure out how to fix this ?
Awesome video.
The only thing that went wrong for me is that when i act as the victim and connect to the AP (fake network) it doesnt redirect me to the login page. It only connects me to the internet and it shows my traffic in the terminal.
I already started apache2 and I put all the files in var/www/html folder.
sir,when i connect fake AP from my target machine it does not show the password portal and it automatically connect AP from target machine
it is my humble request to help me
I really liked the video, but there is a problem: the password window does not appear!
I got the error
dnsmasq: no servers found in /etc/resolv.conf, will retry
like that. Can anyone help me with this. what should I need to edit at /etc/resolv.conf
thanks in advance
shows this error:
root@kali:~/fap# hostapd hostapd.conf
Configuration file: hostapd.conf
nl80211: Could not configure driver mode
nl80211: deinit ifname=wlan0mon disabled_11b_rates=0
nl80211 driver initialization failed.
wlan0mon: interface state UNINITIALIZED->DISABLED
wlan0mon: AP-DISABLED
wlan0mon: CTRL-EVENT-TERMINATING
hostapd_free_hapd_data: Interface wlan0mon wasn’t started
is this error is due to some problem in the adapter?
but my adapter is in monitor mode and is plugged in
Hello there I have tried to perform the attack but I am having 3 types of issue.
1- fake access point not showing in any device after 30-40 seconds
2- when we connect to fake access point not Opening any Upgrade page where user enters their password.
3- many of the time when dns spoof command perfomed it shows that unknown physical layer type 0*323
I have tried it many of the times please give me the solution .
sir i have gone through your ethical hacking course in the wpa2/wpa cracking section iam getiing an error like WPS TRANSICATION FAILED (CODE*03)retrying last pin.Iam getting error countinously . Please help me out from this
install dns masq requirement
Hello,
The video was nice and informative but when i tried it i had one issue
It created fake access point but while connecting to it did not open the template (Firmware Upgrade site)
Please Help
Thankyou