Top 10 Ethical Hacking Tools in 2019
Today I will discuss the top 10 hacking tools used in 2019. These tools can be installed on most operating systems (Windows, Linux or OS X) and are easy to use. I compiled this list of tools based on their usage in industry and success rate during personal use in my Ethical Hacking career.
Before going forward, I want to ask you to please use these tools for legal purposes. I am not responsible for any illegal use of these tools.
Let’s start:
Metasploit
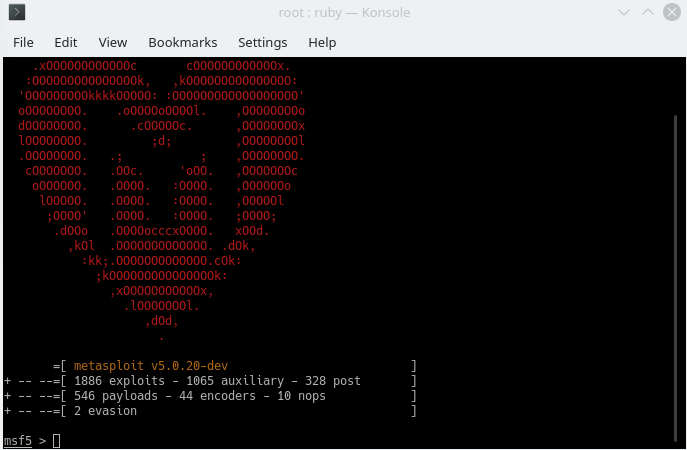
Metasploit is an open-source framework written in Ruby. It can be used in Ethical Hacking for various purposes like testing exploits, scanning for vulnerabilities, post-exploitation and more. It comes pre-installed in Kali but can be installed on most major operating systems such as Windows, Linux and OS X.
Burpsuite
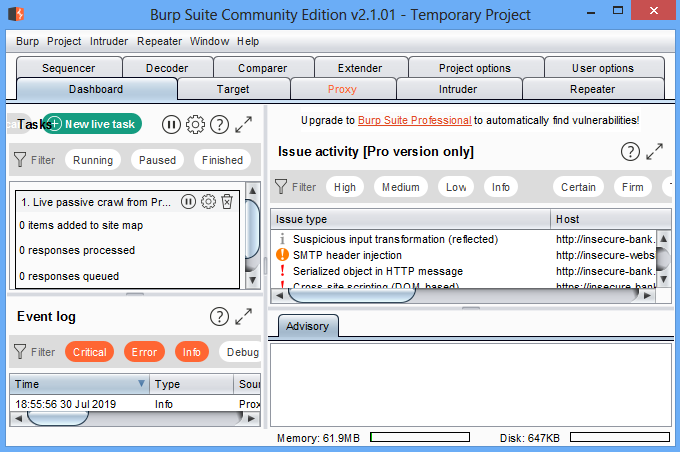
Burpsuite is a modern web application penetration testing framework written in java. It has both free and pro versions. With burp suite you can scan a website for content, find vulnerabilities, exploit them and more! One of the most useful features of it is its famous proxy which can be used to intercept requests to a web application, this is very useful to test for vulnerabilities and bypass security.
Burpsuite is pre-installed in Kali Linux but can be installed on most major operating systems such as Windows, Linux or OS X.
Nmap
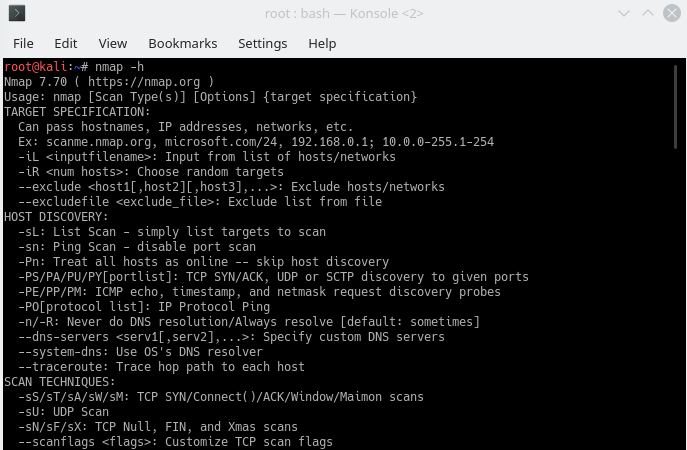
Nmap(Network Mapper) is an open-source tool available for most operating systems, we use it for network discovery and security auditing. Nmap is used by system or network administrators to manage their networks, it can map or discover devices on the network, discover open ports, running services, their operating systems and more!
Nmap has a great feature called NSE(Nmap Scripting Engine) which can be used to automate various tasks that nmap can perform. Nmap is pre-installed in Kali Linux but can be installed on most major operating systems such as Windows, Linux or OS X.
Zenmap
Zenmap is the graphical interface of the Nmap. If you love to use GUI then you’ll love this.
Nping
Nping is another great tool that can be used to generate packets for a wide range of protocols and perform packet analysis.
Wireshark
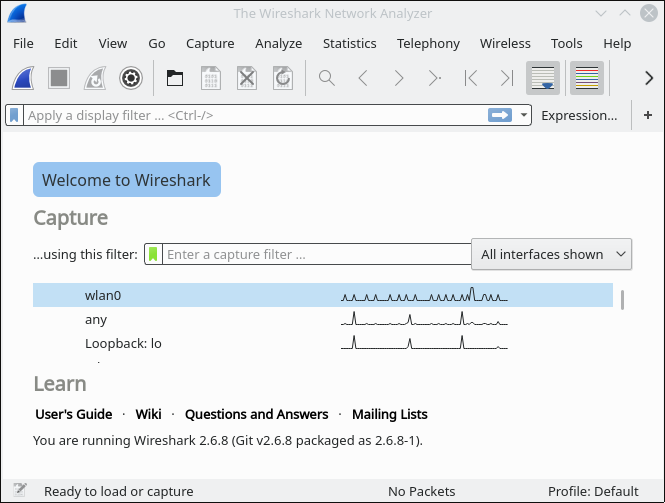
Wireshark is a packet capturing and packet analysis tool, it is great for finding network-level problems, packet sniffing and packet analysis. It can be used to optimize network performance, analyse network traffic …..etc. I personally use Wireshark frequently, it is one of my favourites. It is also per-installed in Kali and is available for most operating systems.
Nessus
Nessus is a huge open-source vulnerability scanning tool that is used to perform vulnerability scans in our penetration testing life cycle. Nessus can find various vulnerabilities, misconfiguration, unauthorised access and more!
Nessus is also available for most operating systems.
Kismet
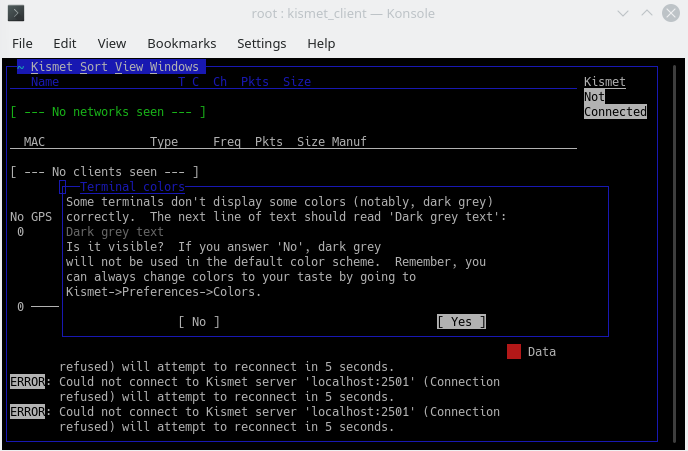
Kismet is great wireless hacking/penetration testing tool, it works with wifi, bluetooth and some SDR (software defined radio), it can be used to discover devices, sniff data, detect intruders and more! It is also pre-installed in Kali and is available for Linux, OSX and Windows.
John the Ripper (JTR)
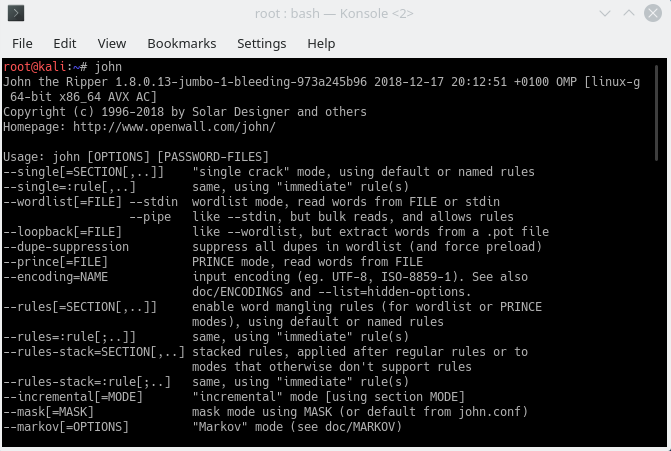
John the ripper is a powerful password cracking tool written in C. The cool thing about it is it can automatically understand which type of encryption is used in a hash. JTR can generate wordlists for you without the need to use another program, perform brute force attacks and crack encrypted passwords, it is pre-installed in Kali Linux and can be installed on most major operating systems such as Windows, Linux or OS X.
Nikto
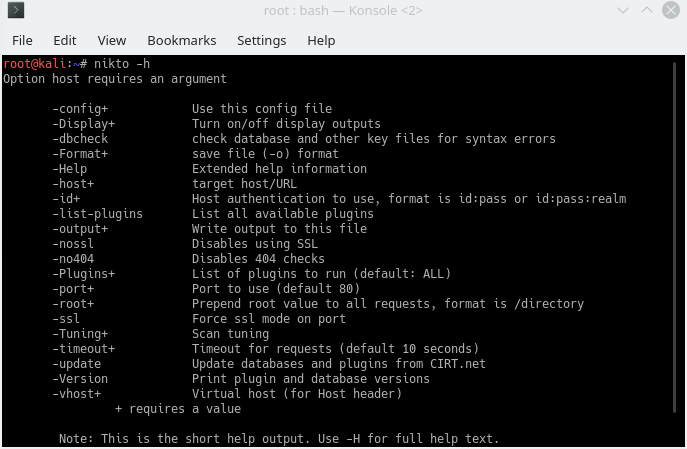
Nikto is an open-source web server vulnerability scanner. According to the Nikto website, it can perform 6700 tests to find dangerous files and programs, check outdated versions, find version-specific problems and discover server misconfigurations. After scanning, it can export scan results to HTML, XML, CSV, and NBE. Nikto can only reliably run on Linux.
Maltego
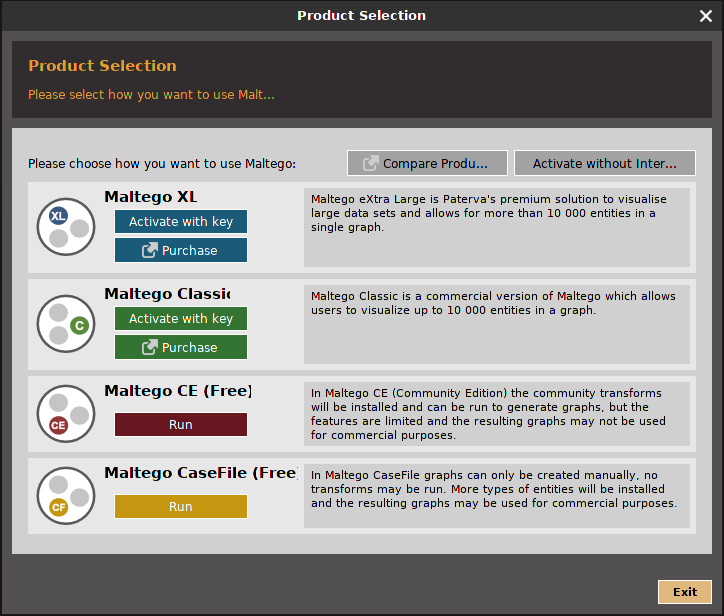
Maltego is an open-source threat assessment software, you can use it for data mining and discovery. It is also referred to as an information-gathering tool. With Maltego, you can gather information about a person, a company, a phone number or any entity you can think of really. It will place the information in a graph which helps to discover and gather even more information and analyze relationships between the discovered entities. Maltego is pre-installed in Kali Linux but can be installed on most major operating systems such as Windows, Linux or OS X.
THC Hydra
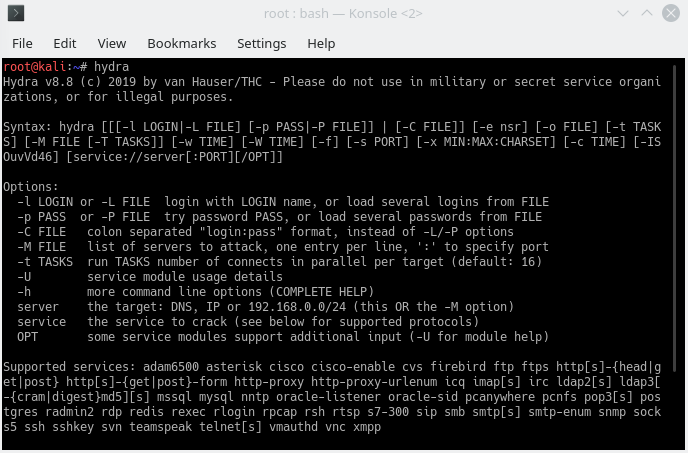
Hydra is a great brute force tool, it is used to run dictionary attacks to guess login information for online services such as HTTP, FTP, SMTP. Unlike JTR Hydra can not generate wordlists and you’ll have to feed it a wordlist to work. THC Hydra is pre-installed in Kali Linux but can be installed on most Linux distros.
Conclusion
So, we have discussed the top 10 ethical hacking tools in my opinion, there are lots of other tools that can do more or less the same job, it really depends on preference and what you’re trying to test, in my opinion though every ethical hacker has to know about these tools and then they can decide whether they want to use these tools, use others or just rely on manual testing.
Leave A Reply
You must be logged in to post a comment.




1 Comment
Nmap is still toping the list.