How to Perform a Phishing (whaling) attack via Emkei’s Fake Mailer
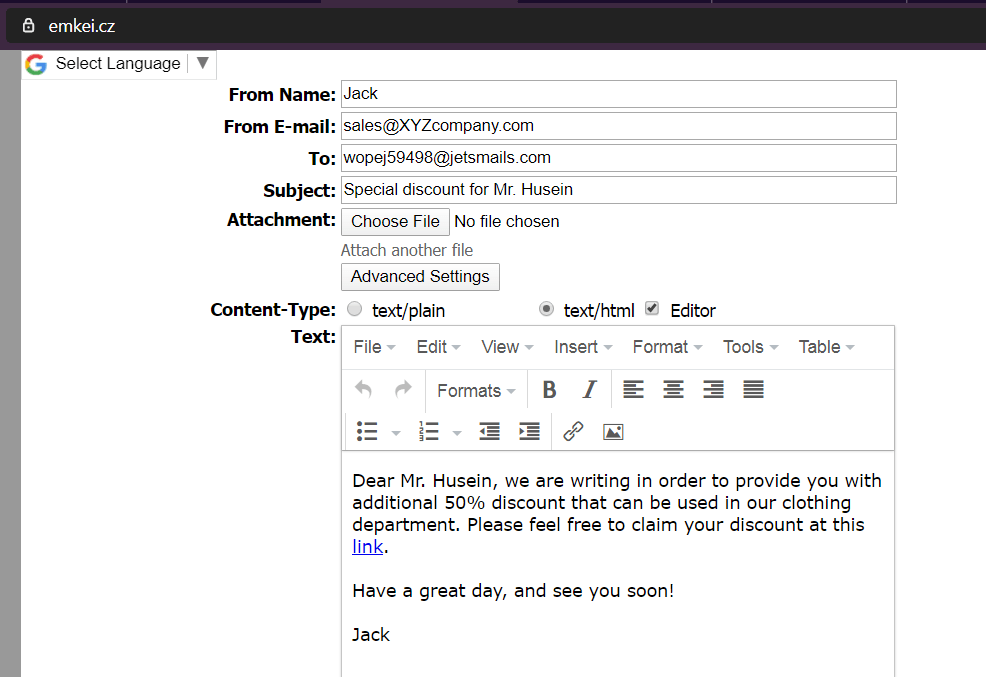
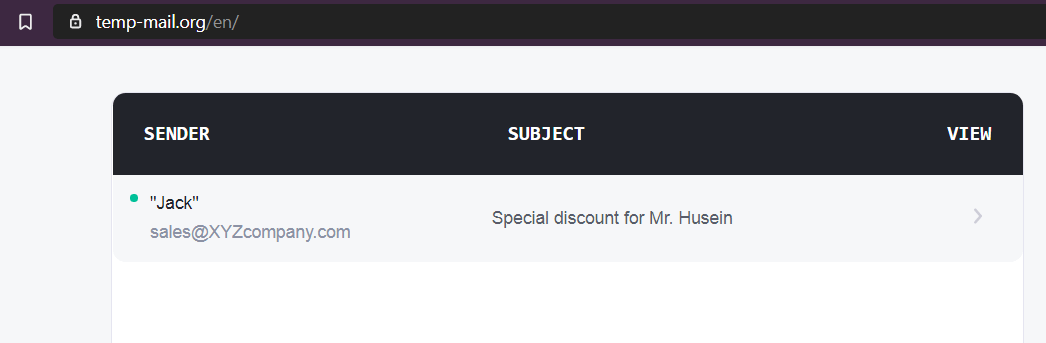
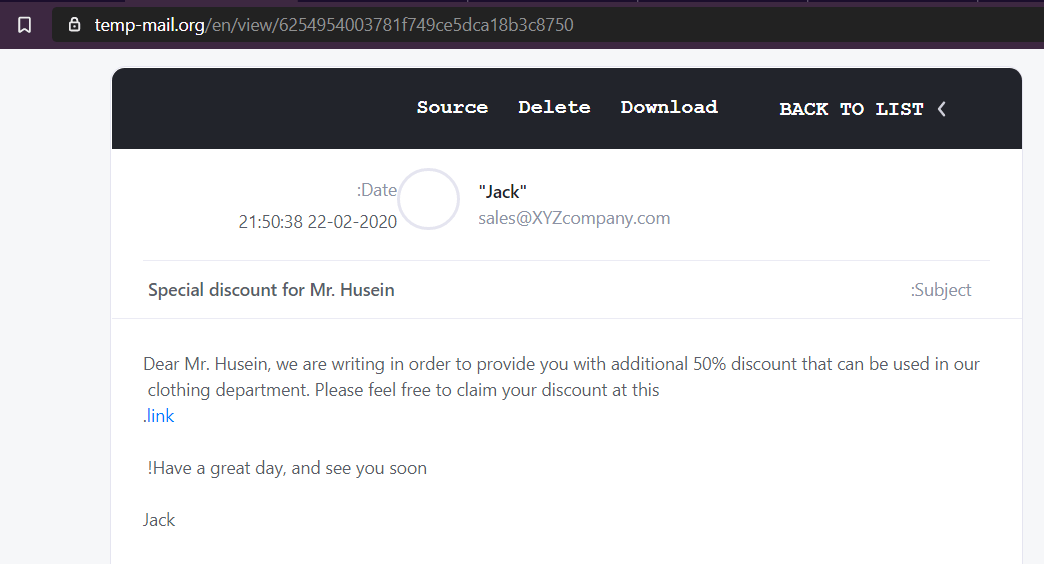
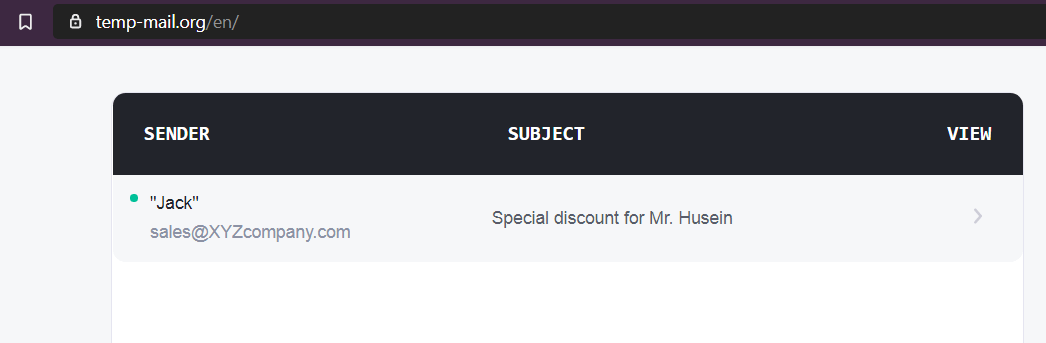
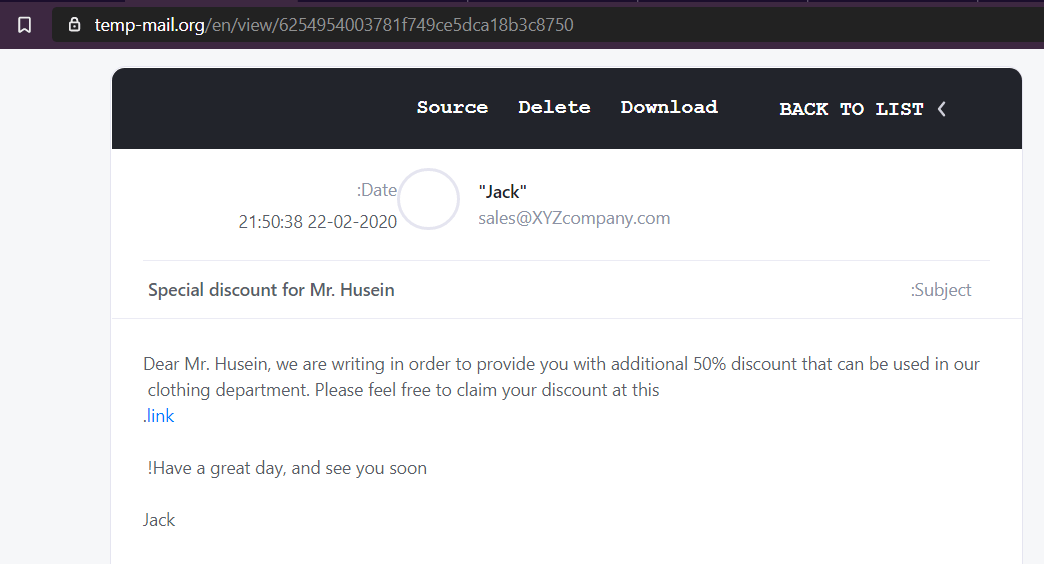
This is how the e-mail should look like in the target inbox:
and
https://temp-mail.org/ – for temporary e-mail address;
Leave A Reply
You must be logged in to post a comment.
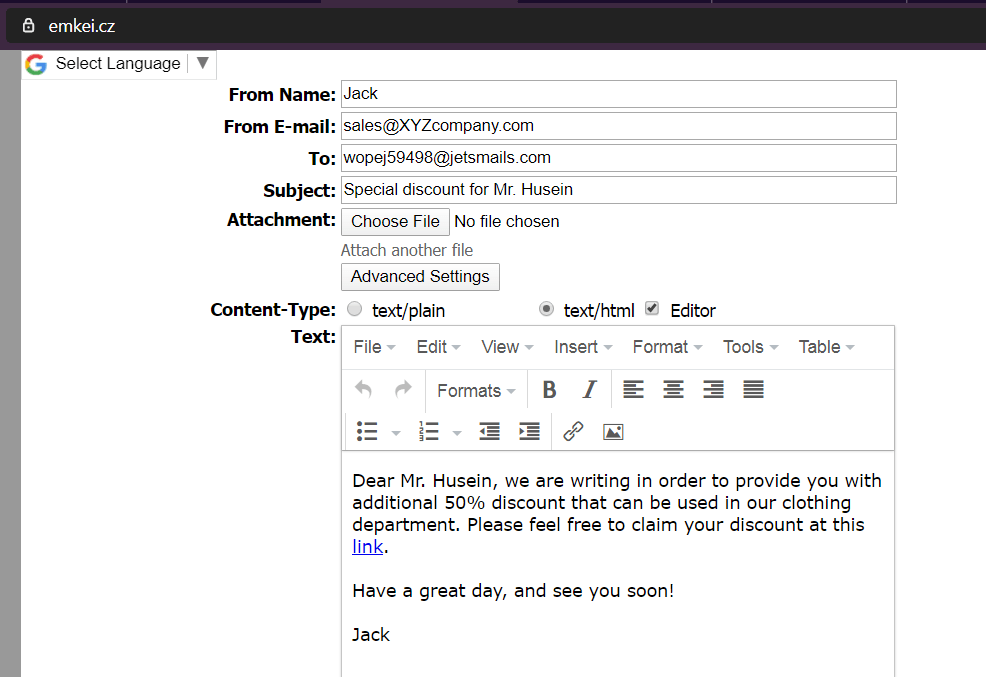
This is how the e-mail should look like in the target inbox:
and
https://temp-mail.org/ – for temporary e-mail address;


You must be logged in to post a comment.
Not a member yet? Register now
Are you a member? Login now
Enroll in this course to access this lesson!
All of our courses include:
✔ Lifetime, unlimited access to course materials & training videos.
✔ Verifiable certificate of completion from zSecurity, signed by the course instructor, Zaid.
✔ Get answers from our Support Team within a maximum of 15 hours.
✔ Unlimited Updates.
Get free 1 month VIP membership per course with:
✔ Live mentorship and Q&A session with the course instructor, Zaid.
✔ Instant support from community members through our private discord channel.
✔ Daily updates with the latest tutorials & news in the hacking world.
✔ Daily resources like CTFs, bug bounty programs, onion services and more!
✔ Access our VIP community & connect with like-minded people.
✔ Discounts on other zSecurity products and services.
3 Comments
Hi Husein,
Thanks for your article. The emails sent from this and using Emkei’s fake mail will automatically be filtered as Spam. Any ideas how to game that?
Best,
Anwar
same issue email marked as spam any solution
Emkei’s smart mailer will mark the mail as spam. Use any other website.