Gathering Information About a Target Website
Hello, today I’m gonna share my knowledge about how to gather information of a website before you attack it or discover any vulnerabilities. Commonly, hackers they call this phase as Reconnaissance. Which means you are going to collect useful information of a website before doing anything else. It is better to check first if it has vulnerabilities just to make sure that the target website is hackable.
Now in order to check if it has any vulnerabilities we need to know the applications, services and technologies it uses, first look for a website that you want to collect the data and to check if it is hackable, make sure you have permission to test the security for this website.
PS: Collecting info as I’m going to show below is not illegal, using any info found to exploit the website is, so you can follow what I’m showing here on any website, but if you are pentesting a website, make sure you have permission to do so.
For example, I’m gonna collect some information about Zaid’s blog, https://za1d.com/.
Go to this website… https://builtwith.com
And input za1d.com (which is your target)……For faster result go here: https://builtwith.com/zaid.com
Note we put the target website after the first forward slash.
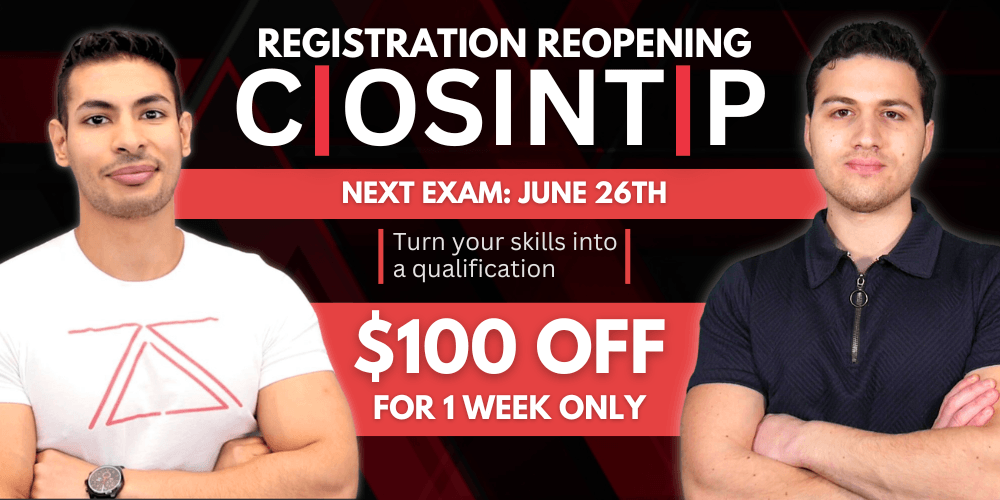
Now this website will check the whole structure of the target website and its frameworks, you’ll get info about the services, web applications, dns information and more about the target, you can now analyze if the website is hackable or not based on this information. It is best method if you apply what you learn in the course available here for website pentesting. Go get the course for Website Hacking by Zaid.
Leave A Reply
You must be logged in to post a comment.




3 Comments
Nice Man 🙂
Alright thanks man for reading…
Thanks for sharing this info!