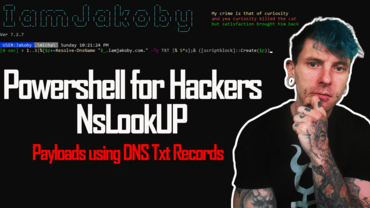
Downloading and executing payloads from DNS Txt Records!
Today I will be covering how to use nslookup to execute scripts from DNS text records stored on your website
This is a concept that was introduced to me by a friend on Twitter.
typically to download and execute scripts we would be using IWR or IEX
but what happens when your target’s PC is using powershell-constrained language which blocks the functionality of these?
if you find yourself doing a pentest for a corporation it’s likely they would have that implemented as a security feature
this is where the nslookup technique comes into play
you see when using nslookup you are not actually downloading anything, you are simply doing a query and executing that output.
Learn how to do that here: