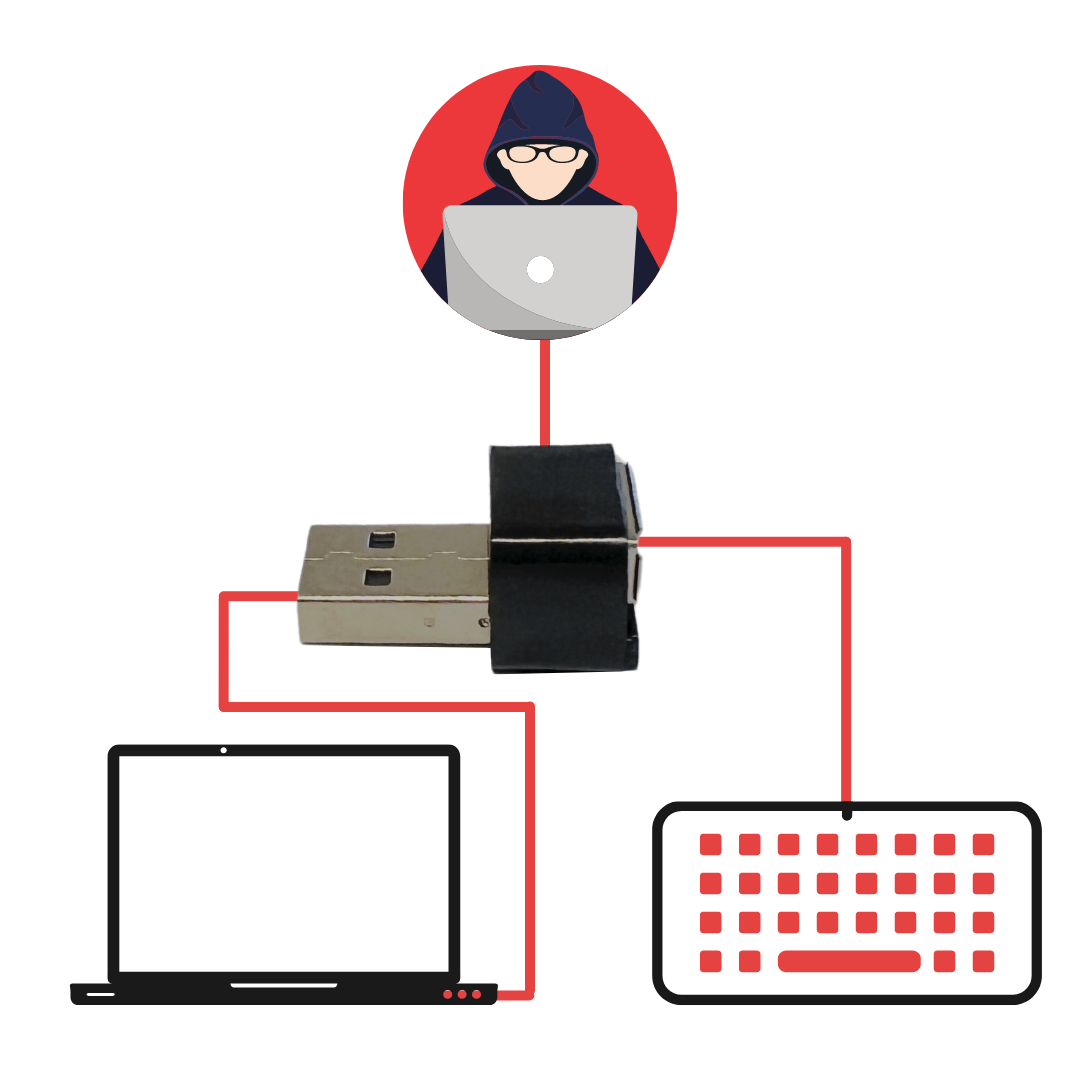
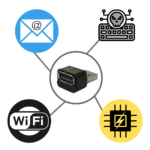
Capture every single button / keystrike from the target computer and access them remotely on cloud, email, UDP or over Wi-Fi.
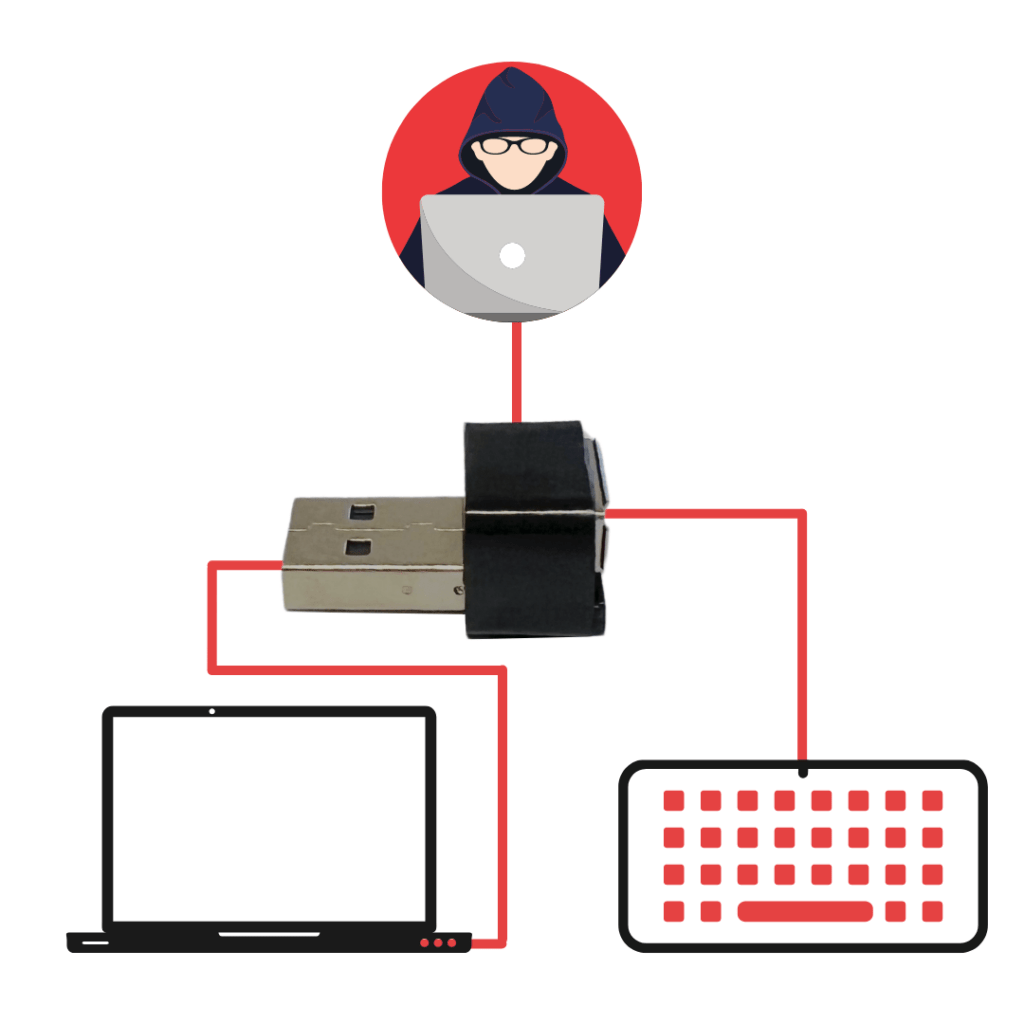
All you have to do is connect the thumb-sized keylogger to a usb port and connect the keyboard to it.
The keylogger will register every single key-strike and store it in its local storage.
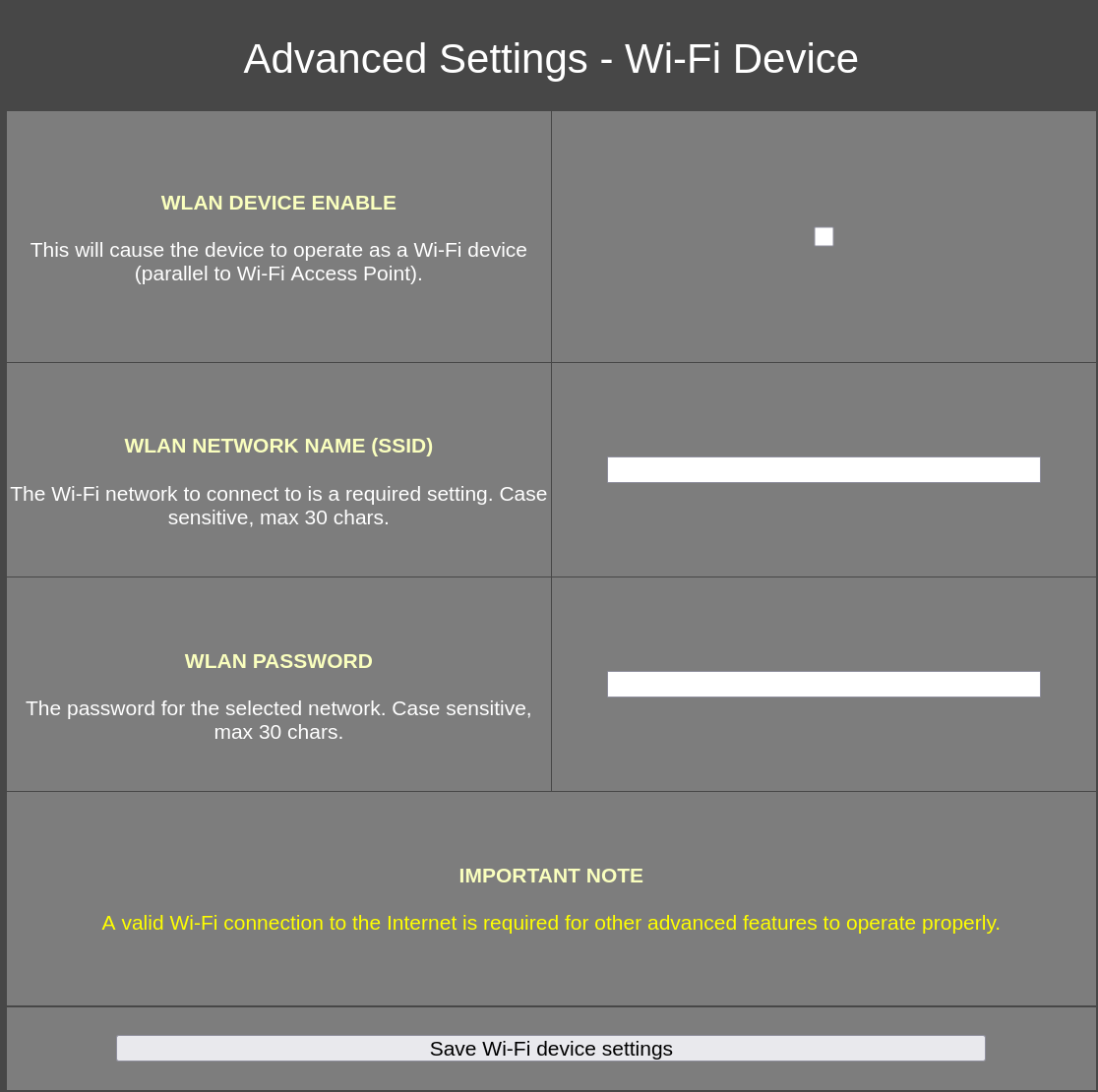
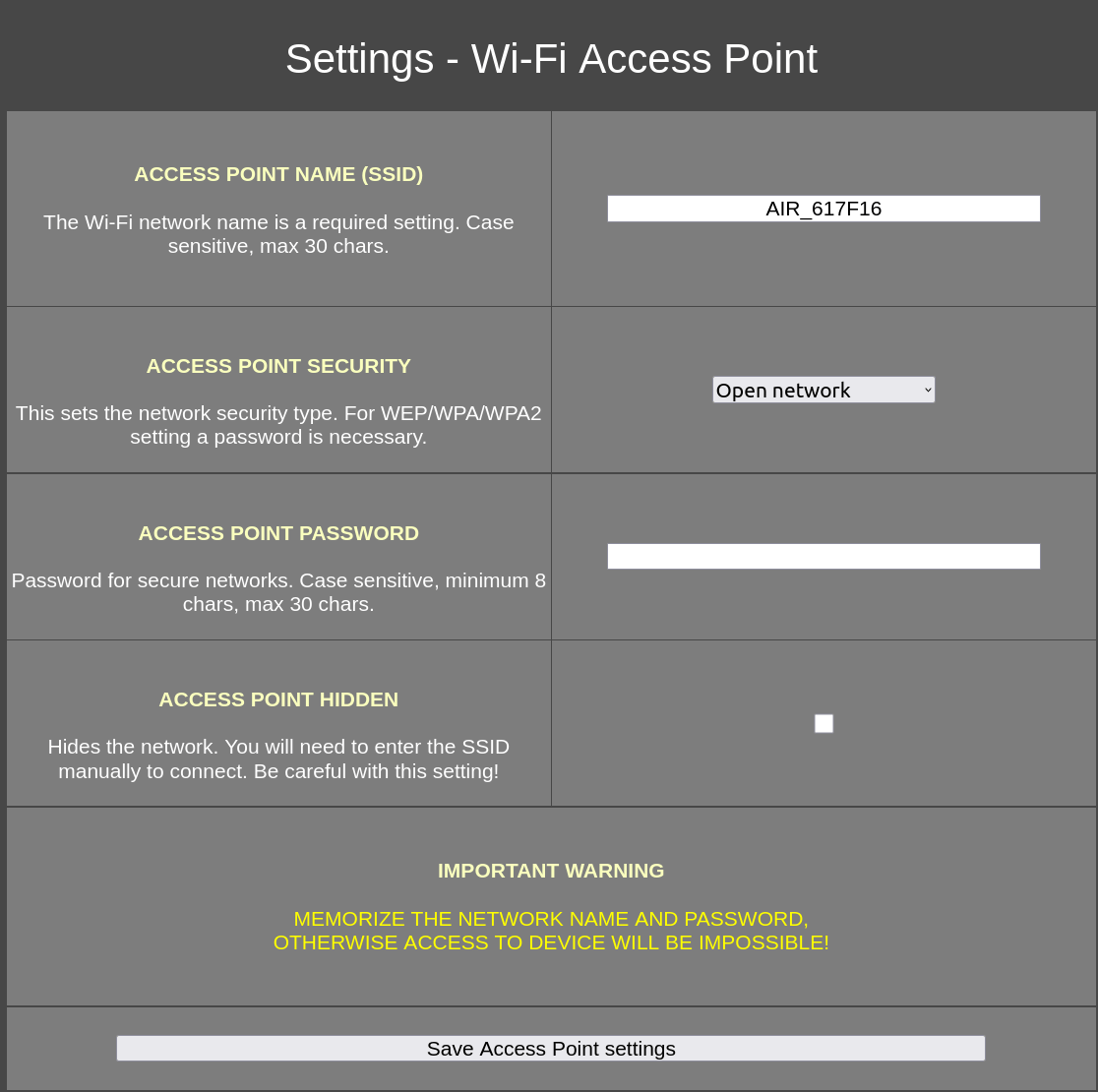
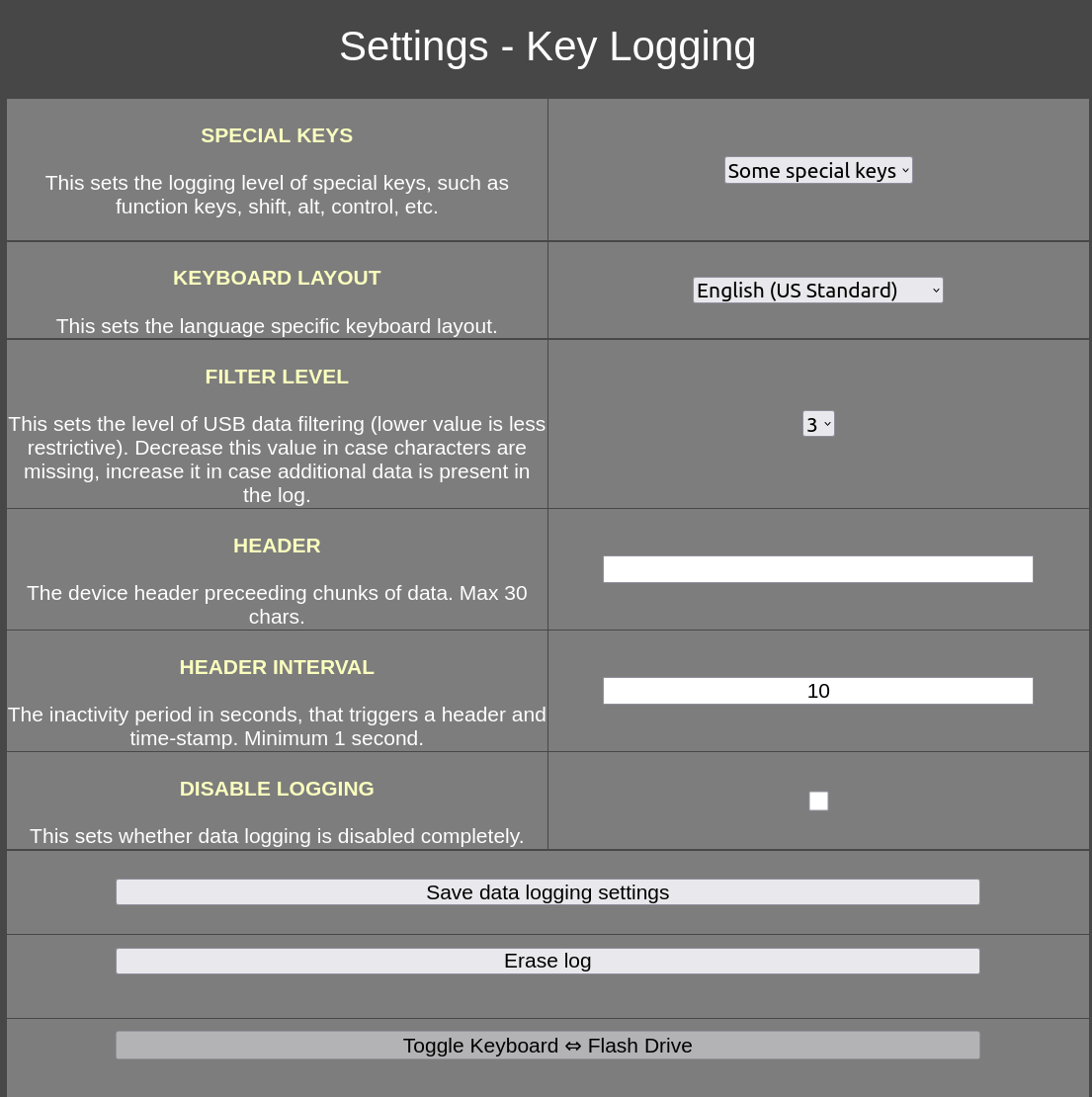
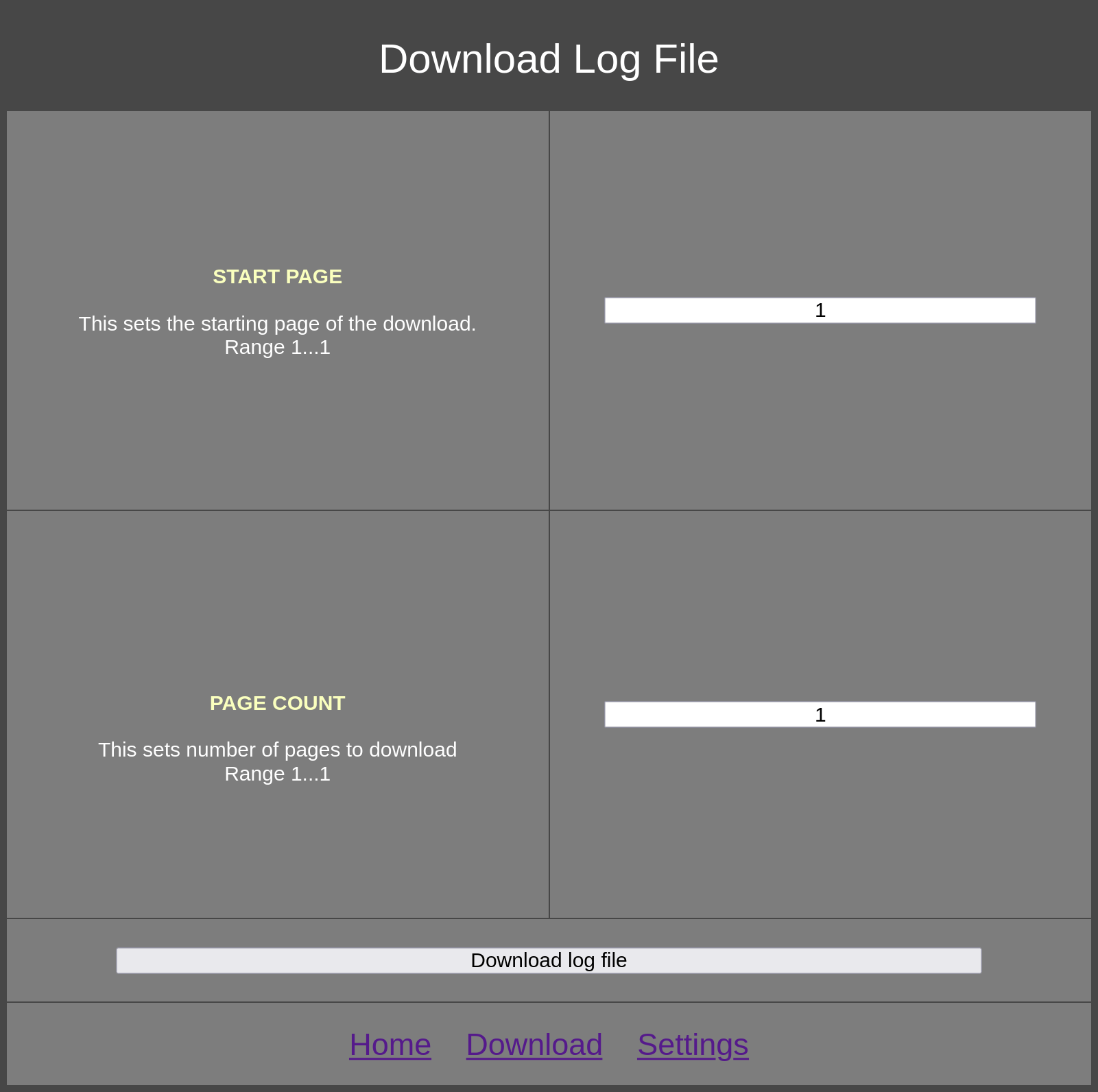
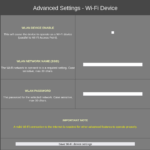
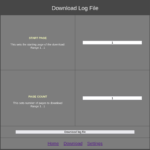
Just like the basic version of the keylogger you can access the collected data and change the keyboard settings over WiFi. Simply connect to the keylogger’s WiFi network and go to http://192.168.4.1
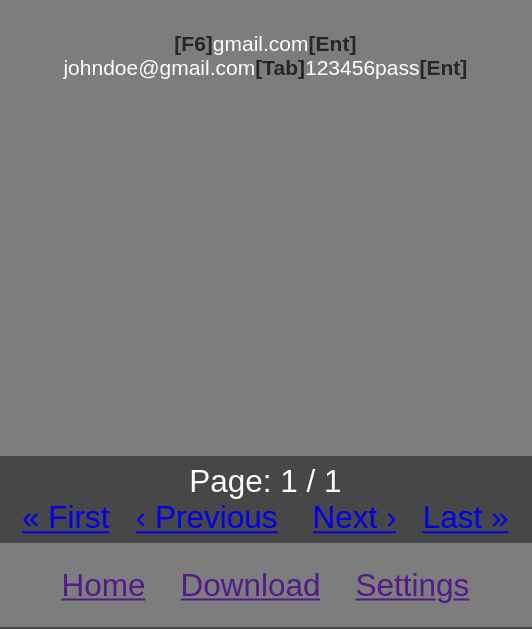
As this is the pro version you also have several other options to access the logs.
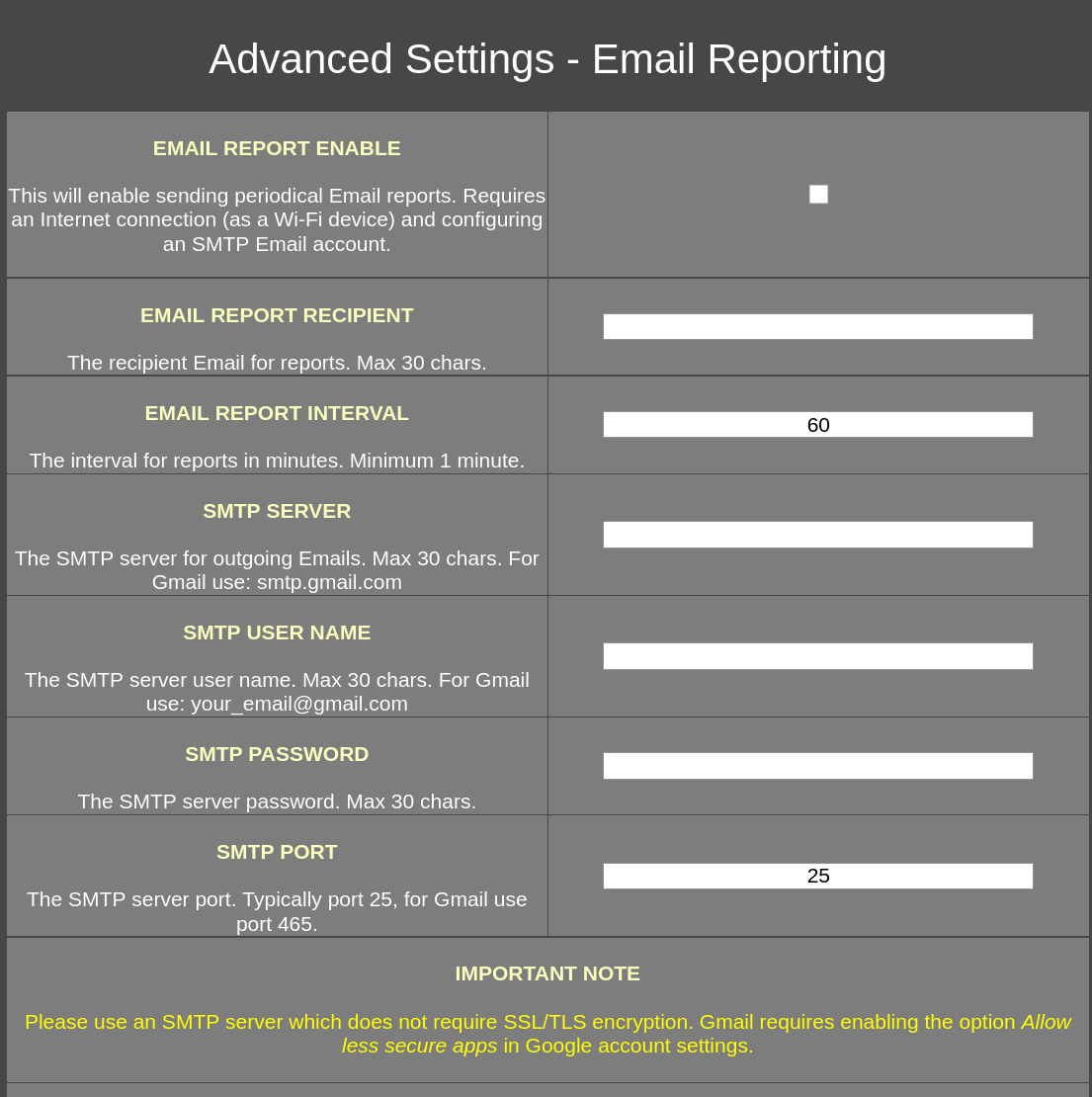
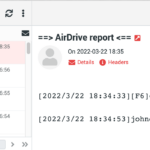
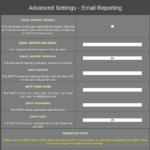
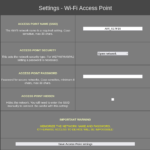
Email Access
1. Connect the device to your computer.
2. Connect to it’s WiFi network.
3. Navigate to http://192.168.4.1/email.html
4. Tick the check box to enable email reporting and fill up your email server information (checkout the next section if you don’t have one).
5. Click Save Email reporting settings to save the settings.
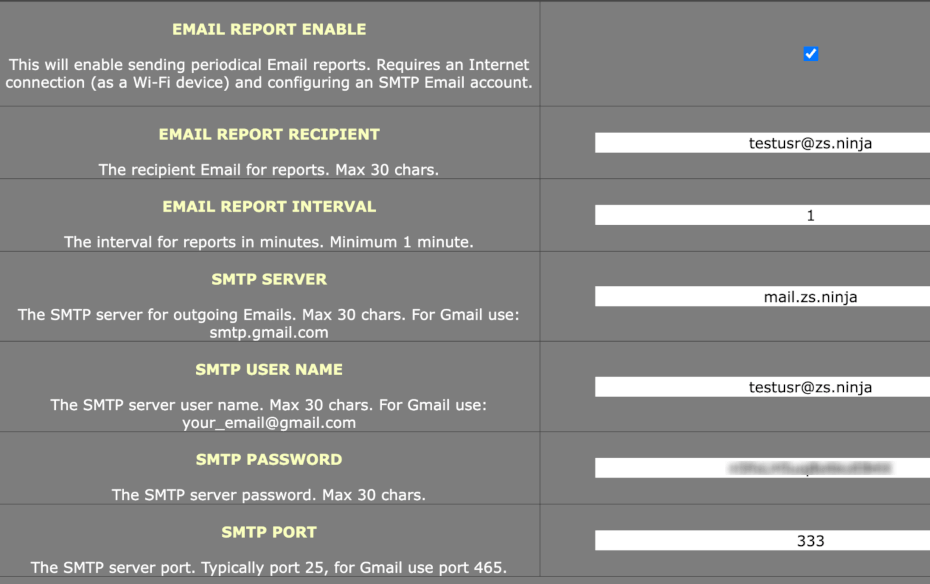
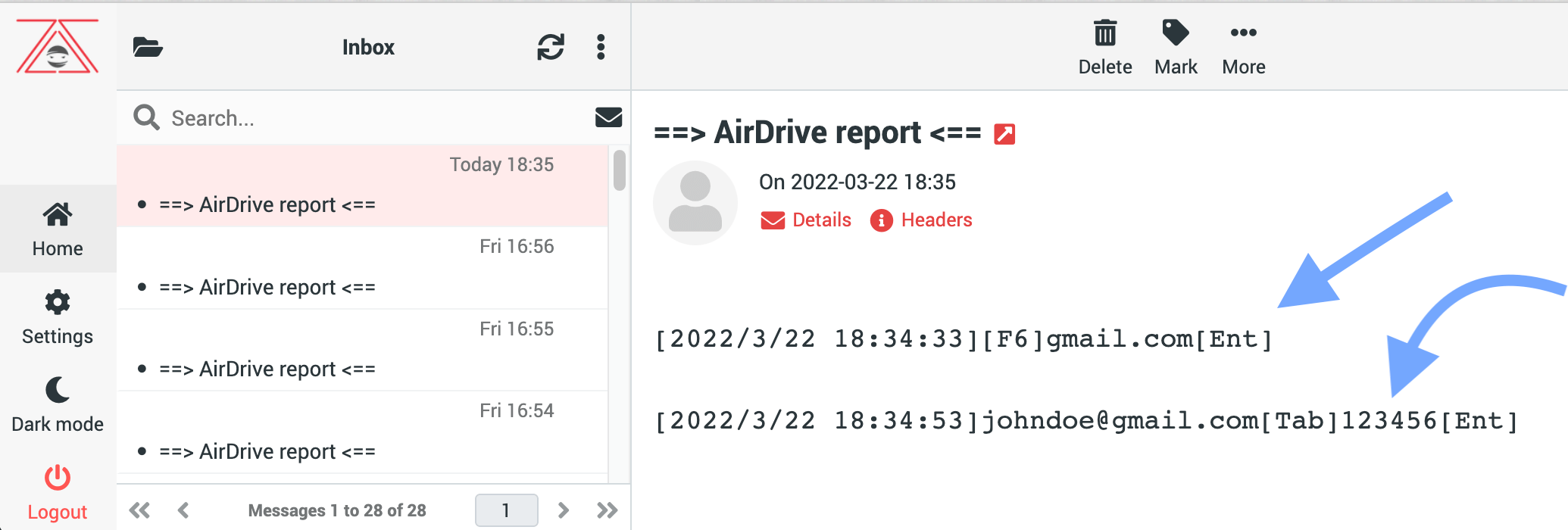
Cloud Access by zSecurity
Once you purchase the device you will receive an automatic email with a username, a password and our mail server information.
Use the information in the email to setup the email reporting settings as shown in the previous section.
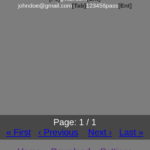
To view the reports, go to zs.ninja and login using the username & password that you got in the email.
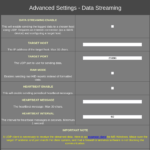
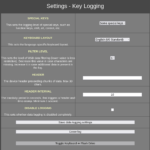
UDP Streaming
With this option you can configure the keylogger to send the key-strikes live as soon as they are pressed to a machine on the cloud!
Machine configuration
You need to listen on a port to receive data from the keylogger, you can use Netcat to do so using the following command
nc -u -l -p 5555
Feel free to replace 5555 with any port you want to listen on.
Keylogger configuration
1. Connect the device to your computer.
2. Connect to it’s WiFi network.
3. Navigate to http://192.168.4.1/streaming.html
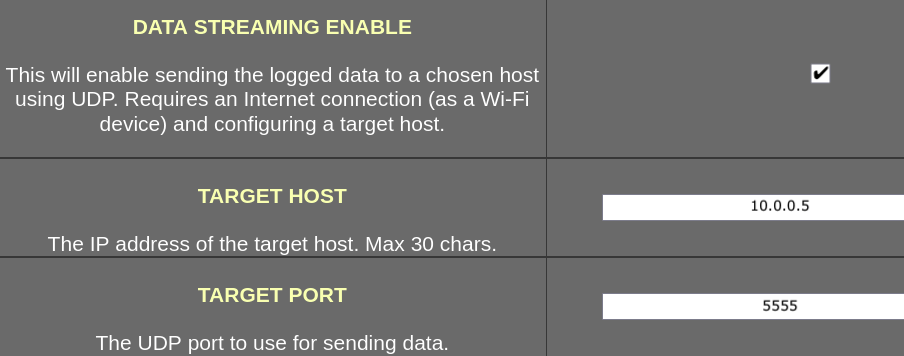
4. Tick the checkbox to enable data streaming.
5. Input the IP of machine that is running Netcat in the TARGET HOST input box.
6. Input the port that Netcat is listening on in the TARGET PORT.
7. Click on Save data streaming settings.
Now when the keylogger is connected to the target’s keyboard, it’ll send the data to Netcat on the fly!









Reviews
There are no reviews yet.