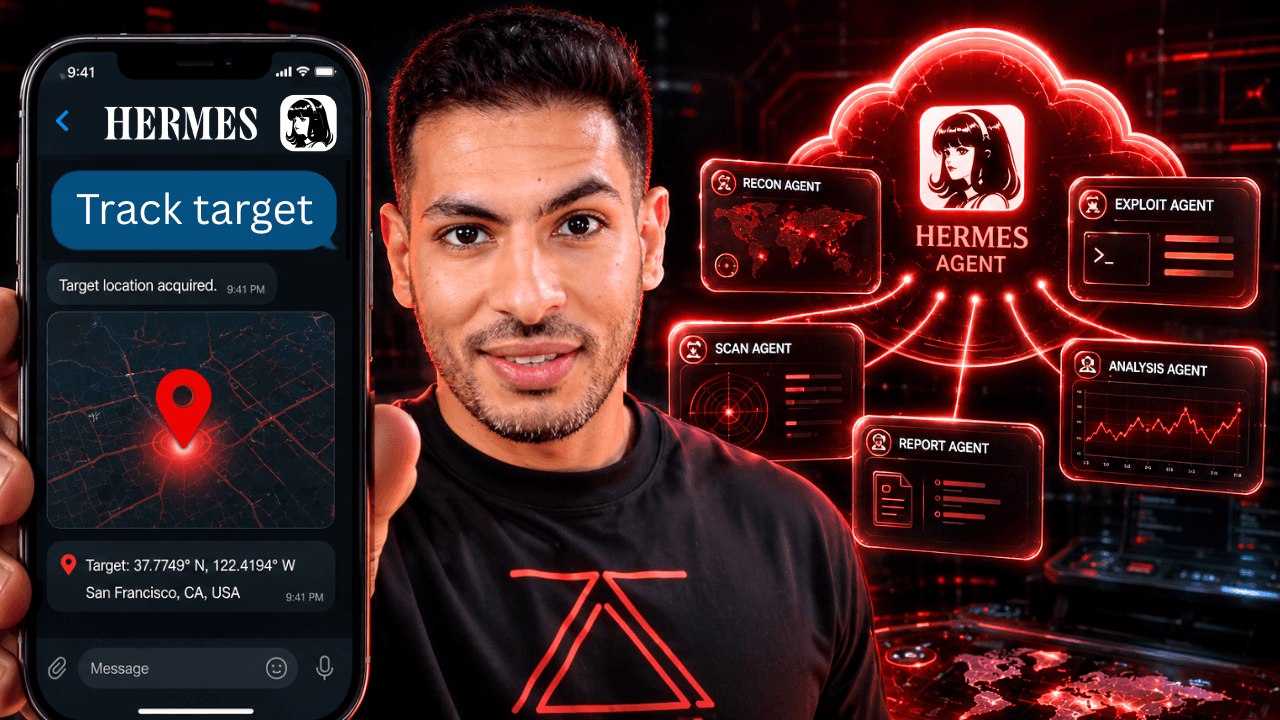
Learn how to build YOUR own cloud-based hacking team that actually uses the terminal and browser to execute your goals. OpenClaw was just the beginning. Hermes Agent is becoming the new standard for agentic frameworks. ✅ C2 via Telegram: Launch …
Learn how to use Prompt Injection to Jailbreak and hack AI through a series of gamified practical labs. Resources: 🔗 Material Security (Sponsor): https://material.security/product/oauth-agent 🔗 Gandalf Labs: https://gandalf.lakera.ai 🔗 Pliny P4RS3LT0NG: https://elder-plinius.github.io/P4RS3LT0NGV3/ 🧠 Learn how to use AI for Hacking …
Build a 24/7 Dark Web & Telegram Breach Monitor to catch leaked and breached passwords instantly In this video you’ll learn how to set up automations to monitor the clear web, dark web, and Telegram for exposed data with instant …
Open Claw has a reputation for being easy to hack, but that usually comes down to an insecure setup. In this video, I walk you through how to properly set up Open Claw for maximum security and privacy. We’ll cover …
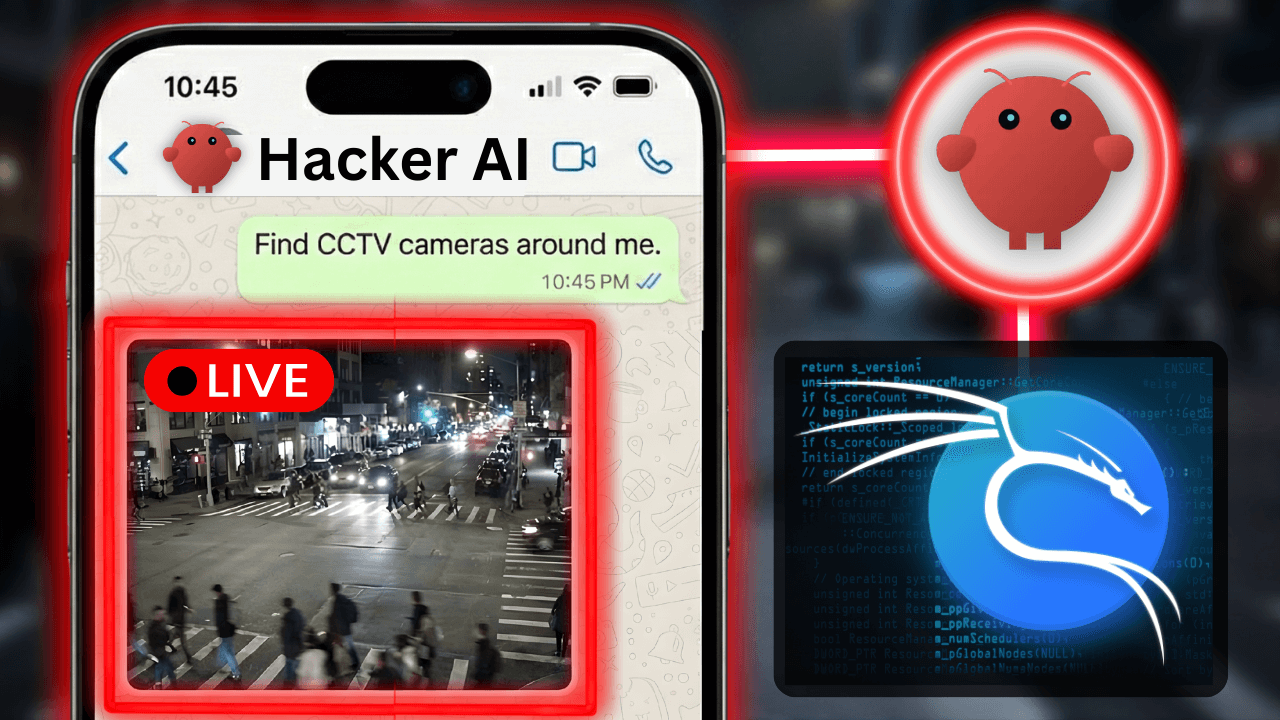
In this video you’ll learn how to build a fully autonomous AI hacking rig using OpenClaw running on a Kali Linux cloud server. Unlike standard AI chatbots, this agent has direct access to tools like Nmap, Metasploit, and the web …
TRACK Instagram Posts – OSINT FREE Tool Hey there, welcome to CyberSudo! I’m Saad Sarraj, and here we break down OSINT and Cyber Security in a simple, beginner-friendly way. In this video, I’ll show you how OSINT investigators can find …