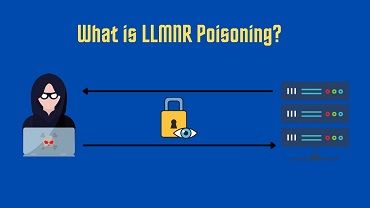
Hey guys, ActiveXSploit back again with a new video, And in today’s video, I am going to explain you LLMNR Poisoning Attack which comes under the Active Directory Exploitation. Thanks for watching Don’t forget to leave a like and subscribe …
Hey guys, In this video, I will talk about reflected XSS that run on live websites. All credits to the researchers who discovered them, and also I’m not responsible for any kind of illegal things, mostly these are normal websites!
Hey guys! In this video, I will briefly explain to you reflected XSS 🙂
Anti-Virus (AV) scanners are that they are there to stop the script kiddies or old malware. If you are using the default settings for Metasploit or using files you downloaded from the internet, chances are that you are going to …
Hi all, In this video, I will be showing you guys how to root the Bank machine from HackTheBox. This was my recorded live Hacking session from the zSecurity VIP Discord Server. If you would like to see more like …
In this video you’ll learn how any USB device such as a normal lamp can be converted to be used to launch a badusb attack, exactly like a rubber ducky or any other HID attack device. This lamp can then …